What Components Are Needed To Form A Dual-port 16-register File Of 8 Bits Each?
1. Elevate DROP. Drag and drop the Ethernet terms from the left onto the correct descriptions on the right.
Select and Place:

Correct Answer:
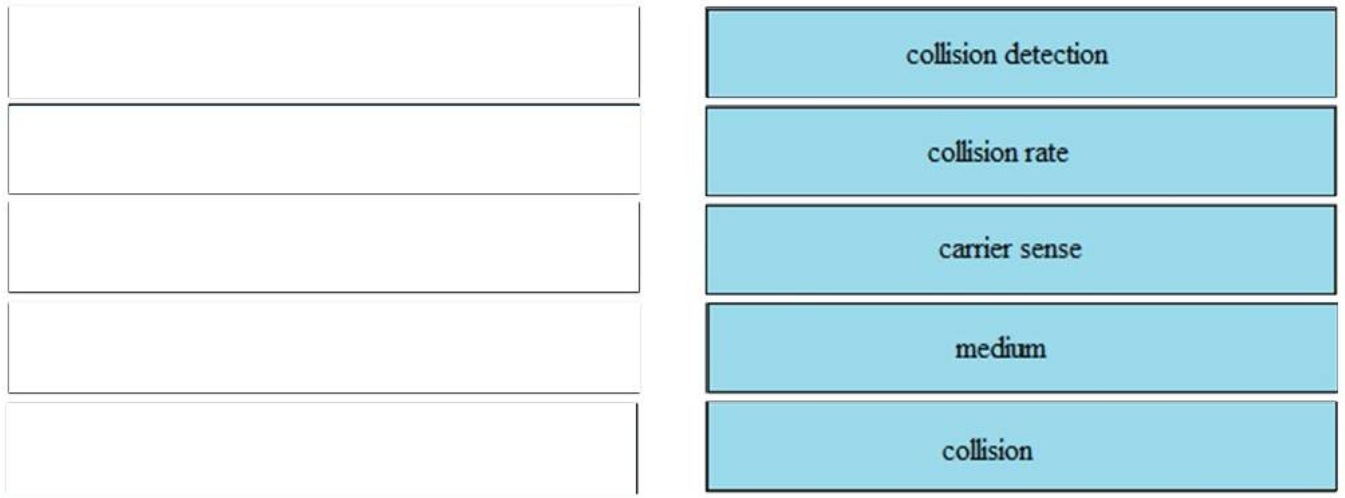
– collision detection: use of CSMA to ensure that devices on a shared link tin can communicate without interfering with ane another
– collision rate: calculated value that tin can increase when a new station is added to a network
– carrier sense: power of an end device to make up one's mind that some other device is communicating on a shared link
– medium: link used to ship data betwixt a source and a destination
– collision: potential conflict when than one end device attempts to send traffic over the aforementioned link
2. DRAG Drib. Refer to the exhibit.
Select and Place:
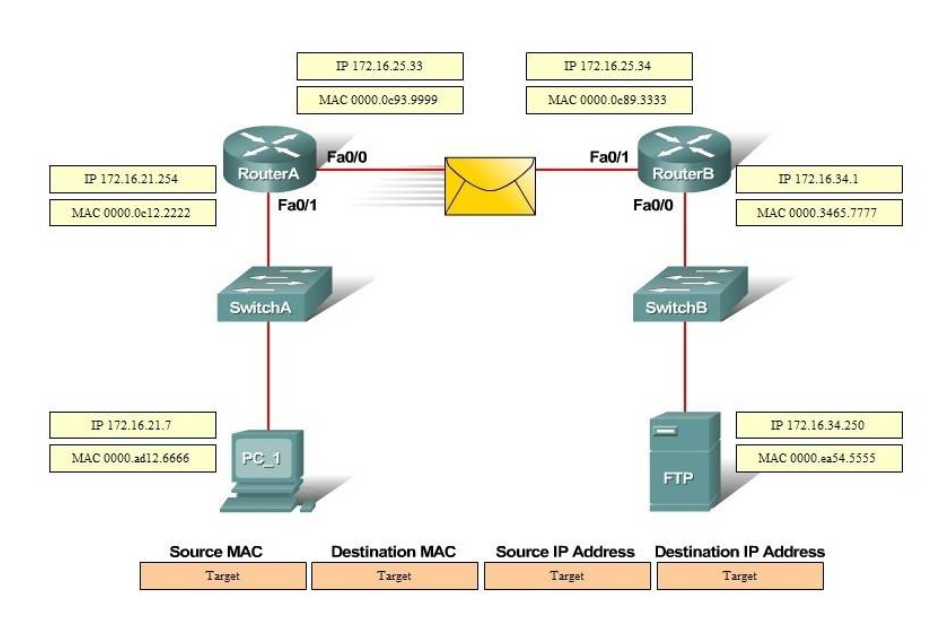
Correct Answer:
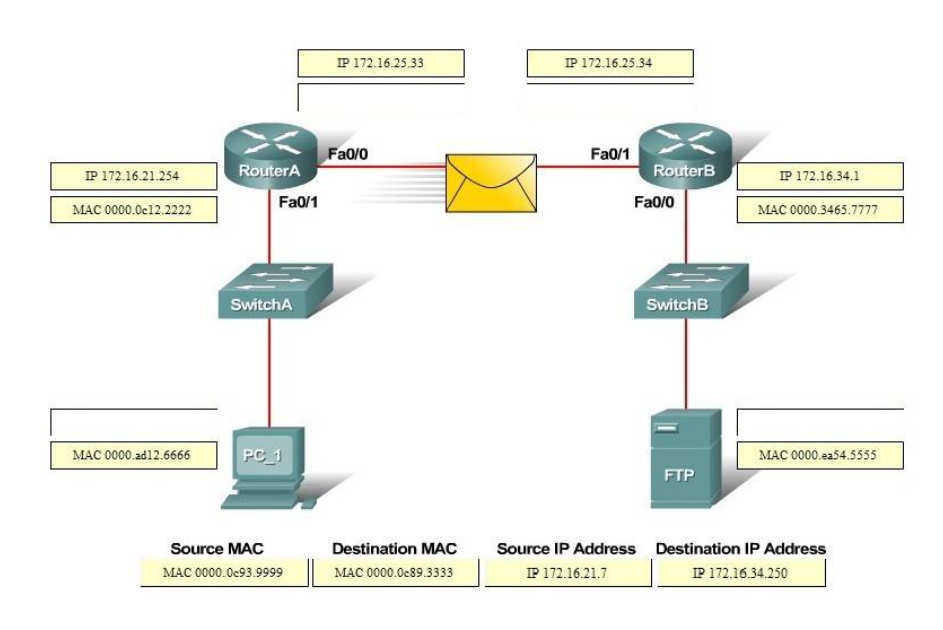
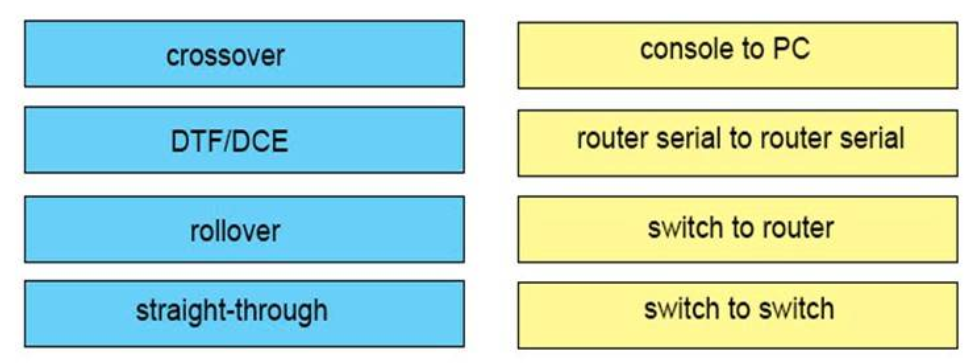
3. Drag DROP. Drag the cable type on the left to the purpose for which is the best suited on the right. Not all options are used.
Select and Place:
Right Answer:
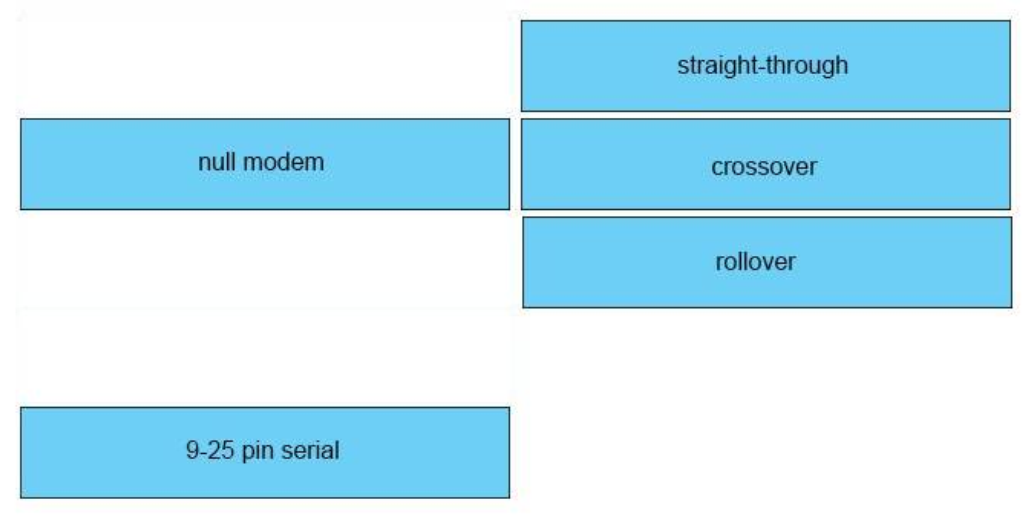
Answer:
+ switch access port to router: straight-through
+ switch to switch: crossover
+ PC COM to switch Console port: rollover
Prove (Hide) Explanation/Reference
To call back which type of cable you should use, follow these tips:
– To connecttwo series interfaces of ii routers nosotros utilizeserial cable
– To specify when we use crossover cable or straight-through cable, we should call back:
Group 1: Router, Host, Server
Group ii: Hub, Switch
One device in group 1 + 1 device in group ii: utilisedirect-through cable
Two devices in the same group: utilizecrossover cable
For case: we use straight-through cable to connect switch to router, switch to host, hub to host, hub to server… and we utilise crossover cablevision to connect switch to switch, switch to hub, router to router, host to host… )
4. DRAG Driblet. Drag the IPv6 multicast accost type on the left to their purpose on the correct..
Select and Identify:
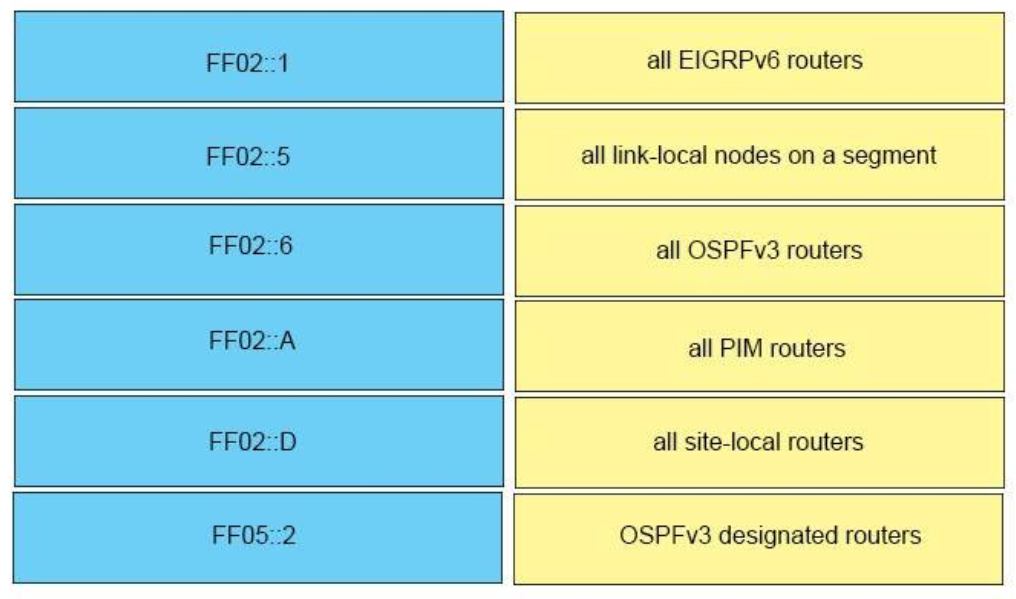
Correct Answer:
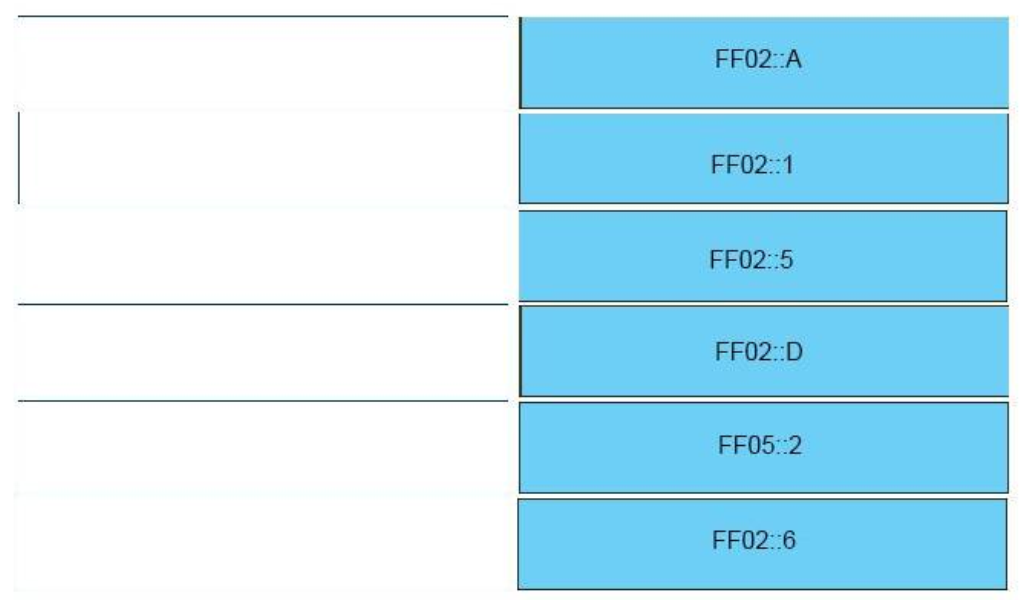
– FF02::A -> all EIGRPv6 routers
– FF02::1 -> all link-local nodes on a segment
– FF02::5 -> all OSPFv3 routers
– FF02::D -> all PIM routers
– FF05::2 -> all site-local routers
– FF02::6 -> OSPFv3 designated routers
v. DRAG DROP. Elevate and drop the IPv6 IP addresses from the left onto the correct IPv6 accost types on the right.
Select and Place:
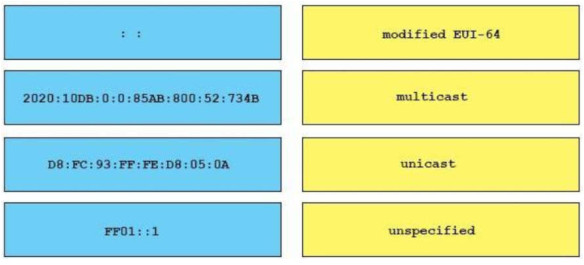
Correct Answer:
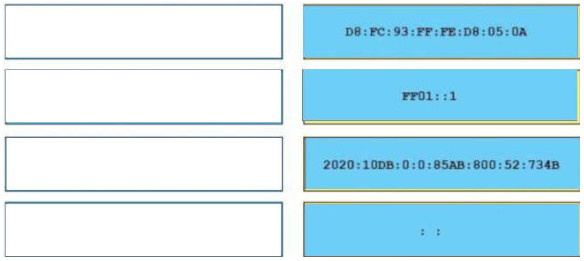
+Modified EUI-64: DB:FC:93:FF:Fe:D8:05:0A
+multicast: FF01::1
+unicast: 2020:10D8:0:0:85:800:52:7348
+unspecified: ::
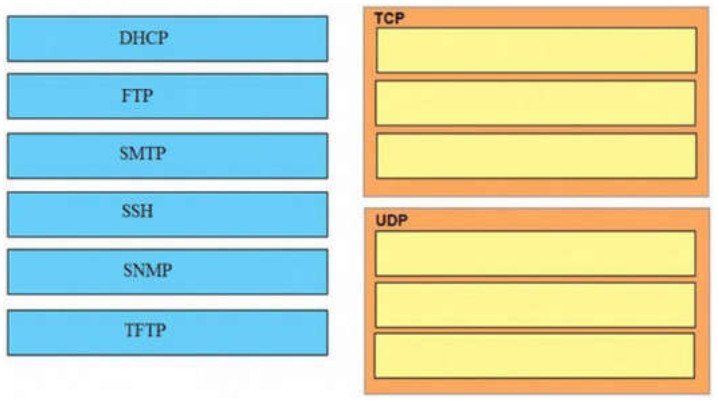
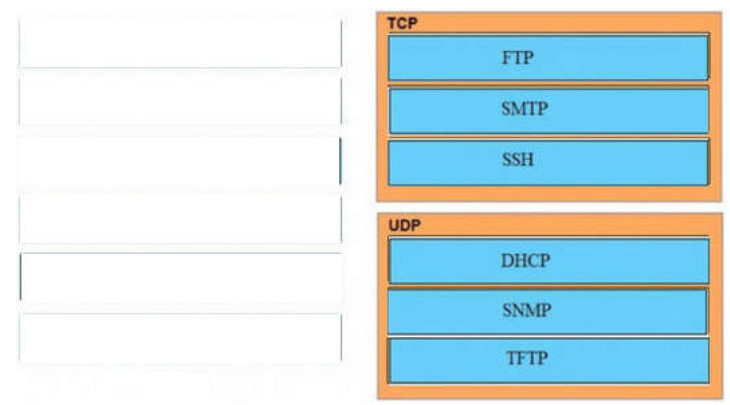
half-dozen. DRAG Driblet. Drag and drop the awarding protocols from the left onto the transport protocols that is uses on the correct.
Select and Identify:
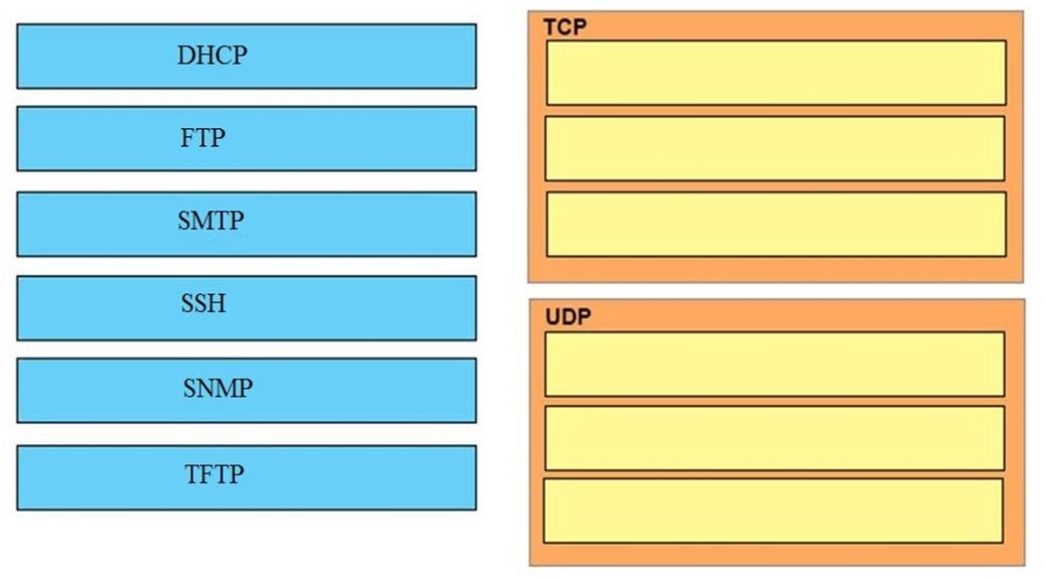
Correct Answer:
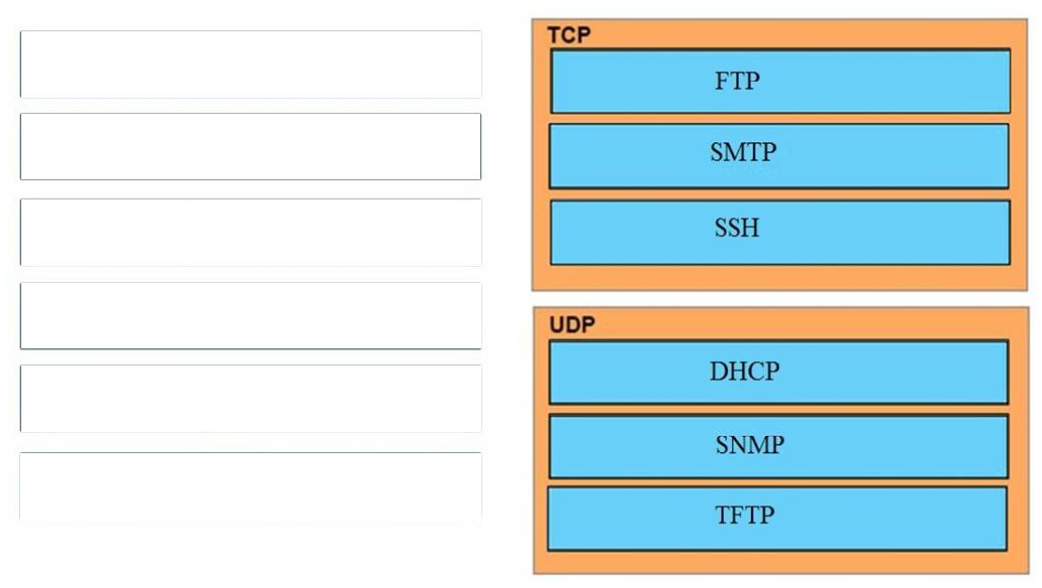
TCP:
+ SMTP
+ SSH
+ FTP
UDP:
+ SNMP
+ DHCP
+ TFTP
7. Elevate Drib. Drag and drop the IEEE standard cable names from the left onto the correct cablevision types on the correct.
Select and Place:
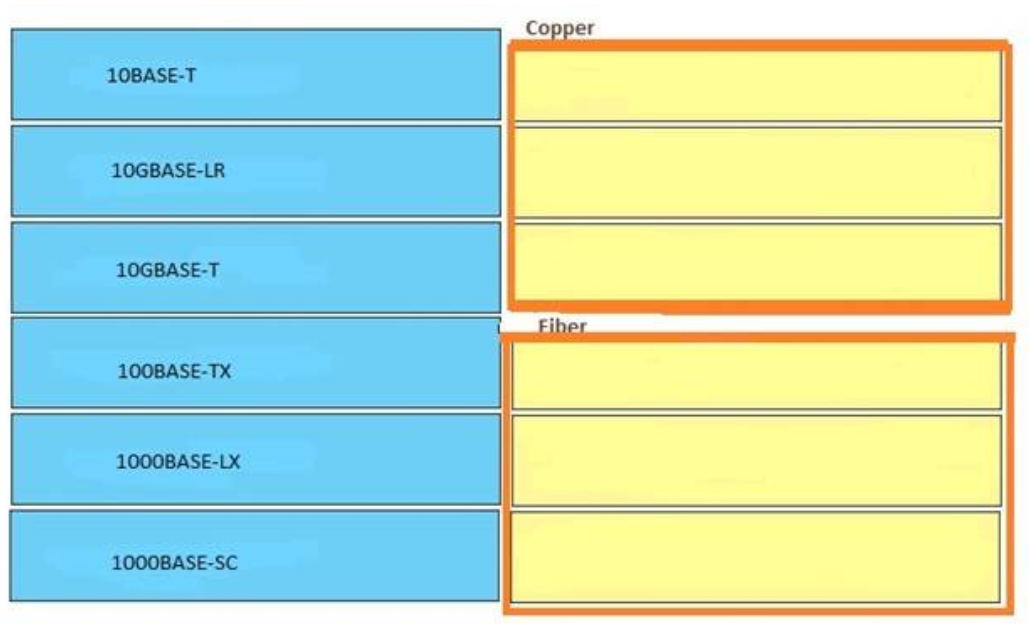
Correct Reply:
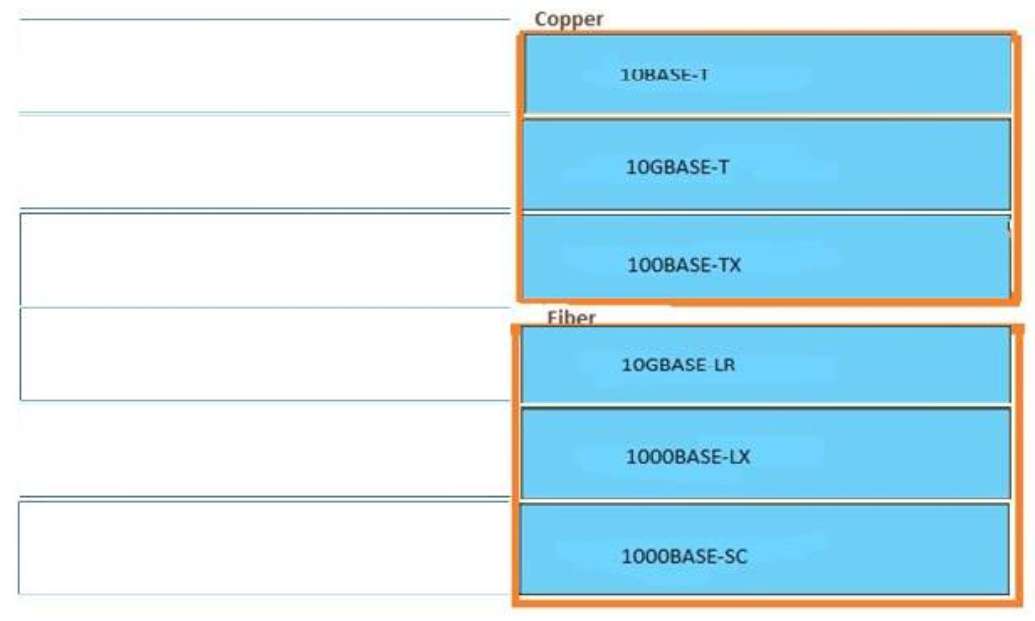
Answer:
Copper:
+ 10BASE-T
+ 100BASE-TX
+ 10GBASE-T
Cobweb:
+ 10GBASE-LR
+ 1000BASE-LX
+ 1000BASE-SC
Show (Hibernate) Explanation/Reference
The "T" letter symbolizes for "twisted pair cable" so all "Base-T…" types are copper.
viii. Drag Drib. A user is unable to connect to the Internet. Based on the layered approach to troubleshooting and beginning with the lowest layer, drag each procedure on the left to its proper category on the right.
Select and Identify:
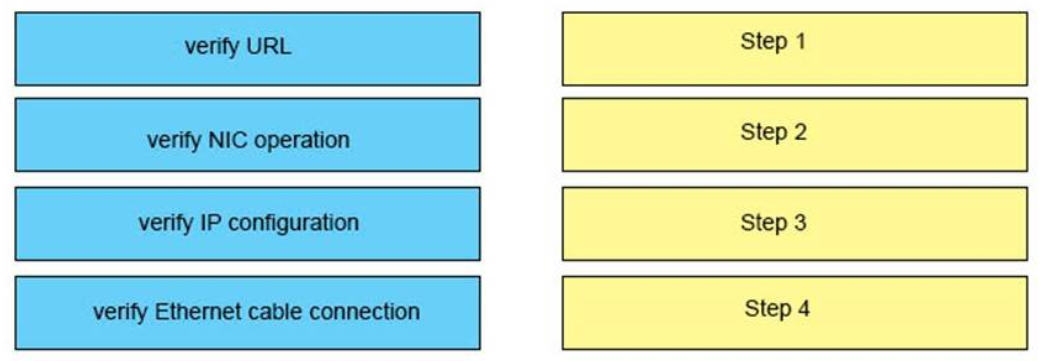
Correct Reply:
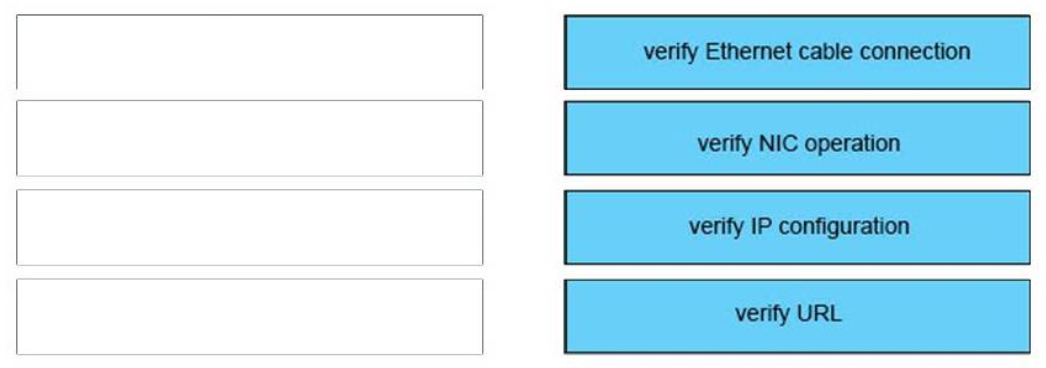
Reply:
1) Verify Ethernet cable connection: Step 1
ii) Verify NIC functioning: Step 2
3) Verify IP configuration: Step 3
4) Verify URL: Step 4
Testify (Hibernate) Caption/Reference
The question asks u.s.a. to "begin with the lowest layer" then we have to begin with Layer 1: verify physical connection; in this case an Ethernet cable connexion. For your information, "verify Ethernet cable connection" ways that we bank check if the type of connection (crossover, straight-through, rollover…) is correct, the RJ45 headers are plugged in, the indicate on the cable is acceptable…
Next we "verify NIC operation". Nosotros do this by just making a ping to the loopback interface 127.0.0.1. If it works then the NIC card (layer 1,2) and TCP/IP stack (layer iii) are working properly.
Verify IP configuration belongs to layer 3. For example, checking if the IP can be assignable for host, the PC's IP is in the same network with the gateway…
Verifying the URL by typing in your browser some pop websites like google.com, microsoft.com to assure that the far end server is not downward (information technology sometimes make we think we can't access to the Cyberspace). We are using a URL so this step belongs to layer 7 of the OSI model.
ix. Drag DROP. Drag the terms on the left onto the appropriate OSI layer on the right. (Not all options are used.)
Select and Place:
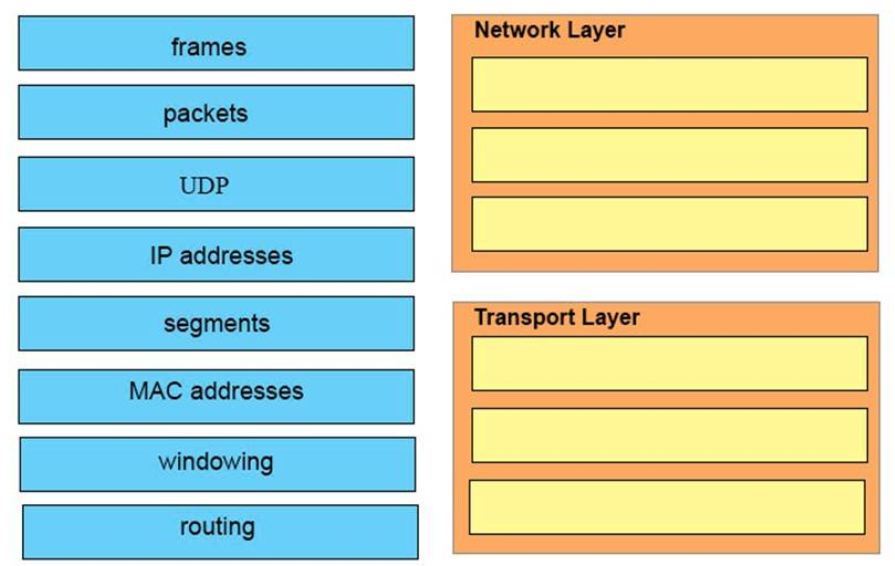
Correct Answer:
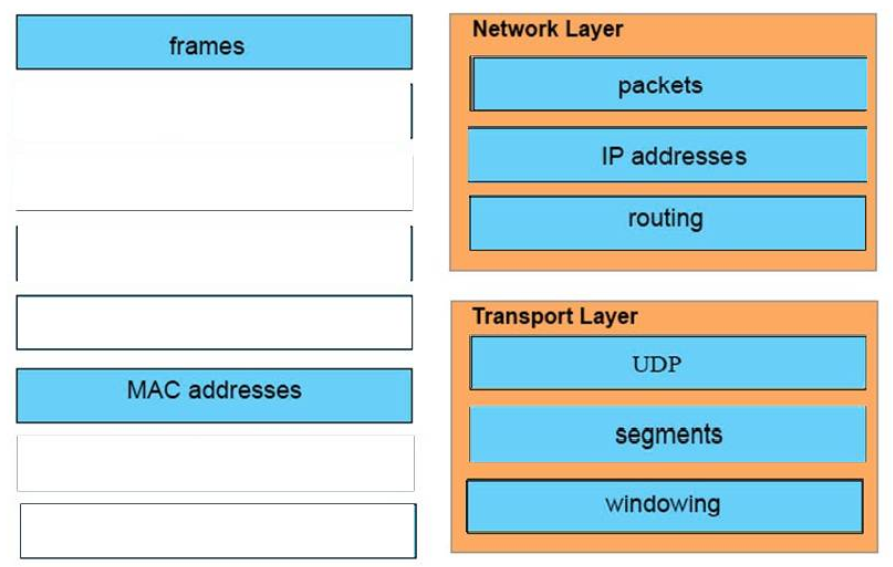
Answer:
Network Layer:
+ packets
+ IP address
+ routing
Transport Layer:
+ udp
+ segments
+ windowing
10. DRAG DROP. Refer to the exhibit.
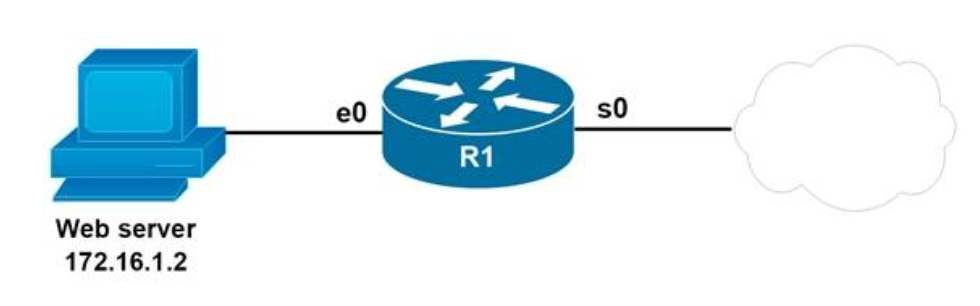
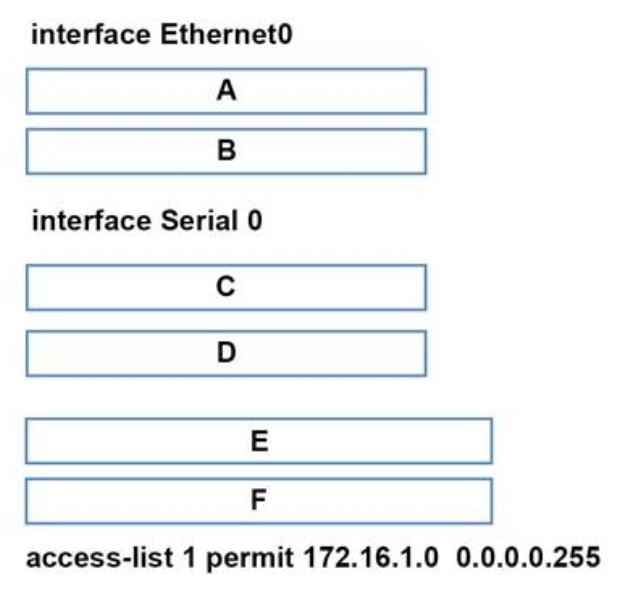
You are configuring the router to provide Static NAT for the web server.
Drag and drop the configuration commands from left onto the messages that correspond to its position in the
configuration on the right.
Select and Place:
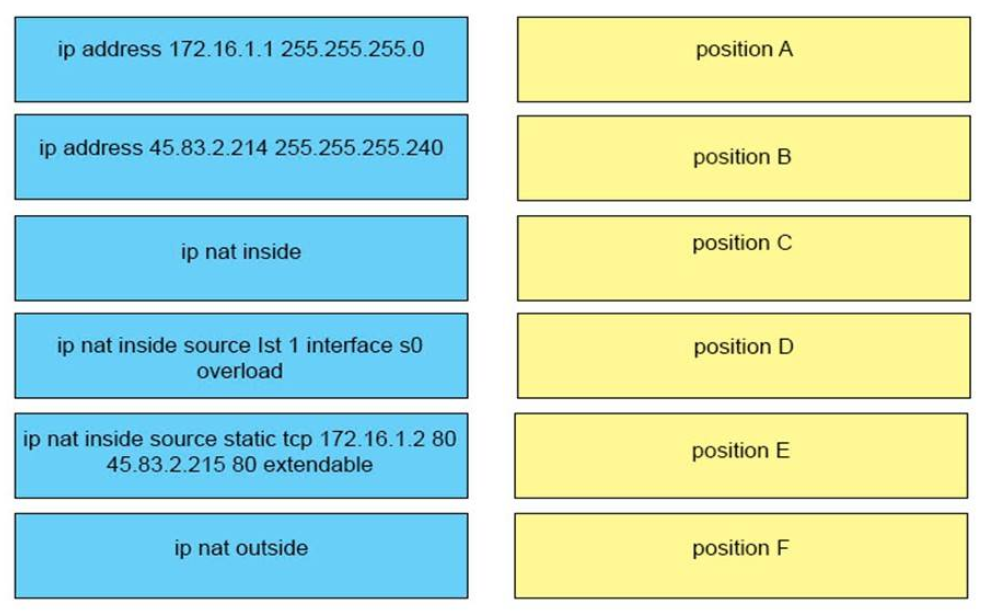
Correct Answer:
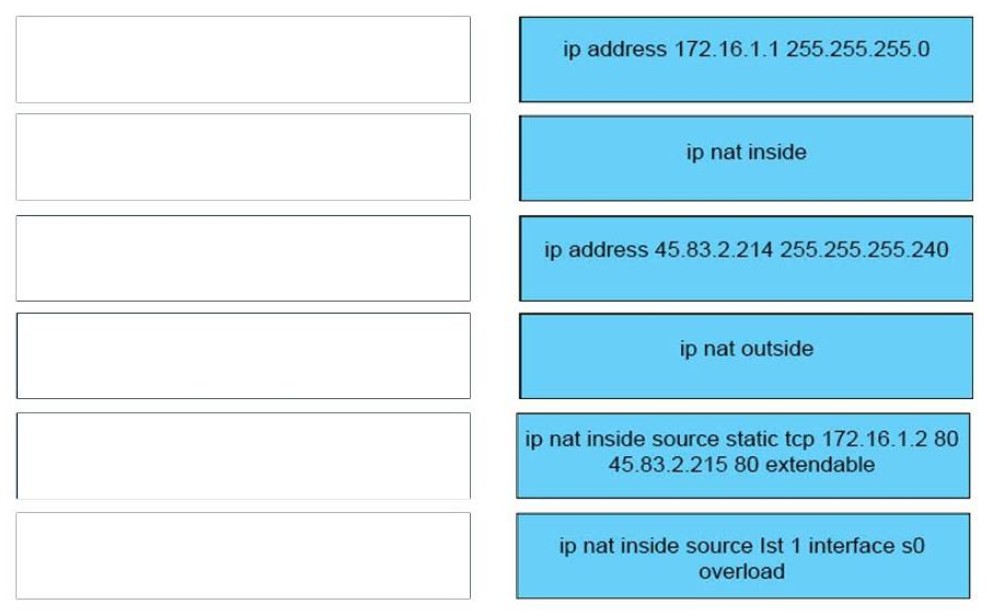
+ position A: ip address 172.16.1.1 255.255.255.0
+ position B: ip nat inside
+ position C: ip accost 45.83.2.214 255.255.255.240
+ position D: ip nat outside
+ position E: ip nat inside source static tcp 172.xvi.1.ii 80 45.83.ii.215 lxxx extendable
+ position F: ip nat within source Ist 1 interface s0 overload
xi. DRAG DROP. Drag and drop each cable blazon from the left onto the blazon of connectedness for which information technology is best suited on the right.
Select and Place:
Correct Reply:
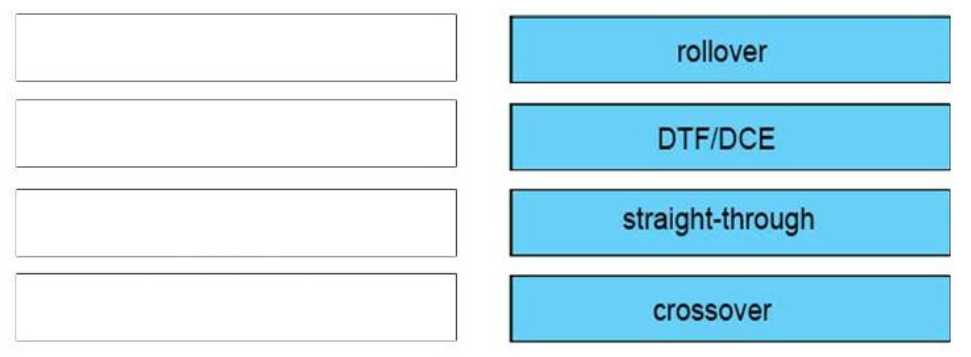
Answer:
crossover: switch to switch
DTE/DCE: Serial to Series
straight-through: PC to router
rollover: PC to Panel
Evidence (Hide) Explanation/Reference
To remember which type of cable yous should utilise, follow these tips:
– To connectii series interfaces of 2 routers we useserial cable
– To specify when we utilize crossover cable or straight-through cablevision, we should think:
Group 1: Router, Host, Server
Grouping ii: Hub, Switch
One device in grouping 1 + One device in group 2: applystraight-through cable
Two devices in the same grouping: applycrossover cable
For example: nosotros apply straight-through cable to connect switch to router, switch to host, hub to host, hub to server… and nosotros use crossover cable to connect switch to switch, switch to hub, router to router, host to host… )
Note: The right cable blazon of PC – Router should be crossover. But it was utilise for switch – switch (which is surely correct) and then this question contains a bug.
12. Drag Drib. Drag and driblet the characteristics of a cloud surround from the left onto the correct examples on the right
Select and Place:
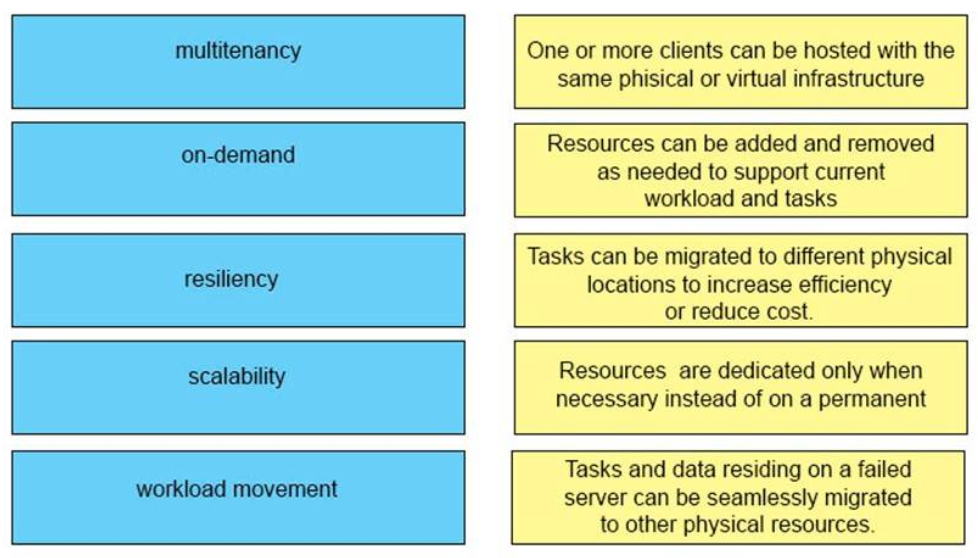
Right Answer:

Answer:
+ Multitenancy: One or more clients tin can be hosted with the same physical or virtual infrastructure
+ Scalability: Resources can be added and removed as needed to back up current workload and tasks
+ Workload movement: Tasks can be migrated to dissimilar physical locations to increase efficiency or reduce cost
+ On-demand: Resource are dedicated merely when necessary instead of on a permanent basis
+ Resiliency: Tasks and information residing on a failed server can exist seamlessly migrated to other concrete resource
13. Drag Drop. Elevate and drop each circulate IP address on the left to the Broadcast Accost column on the right. Non alloptions are used.
Select and Place:
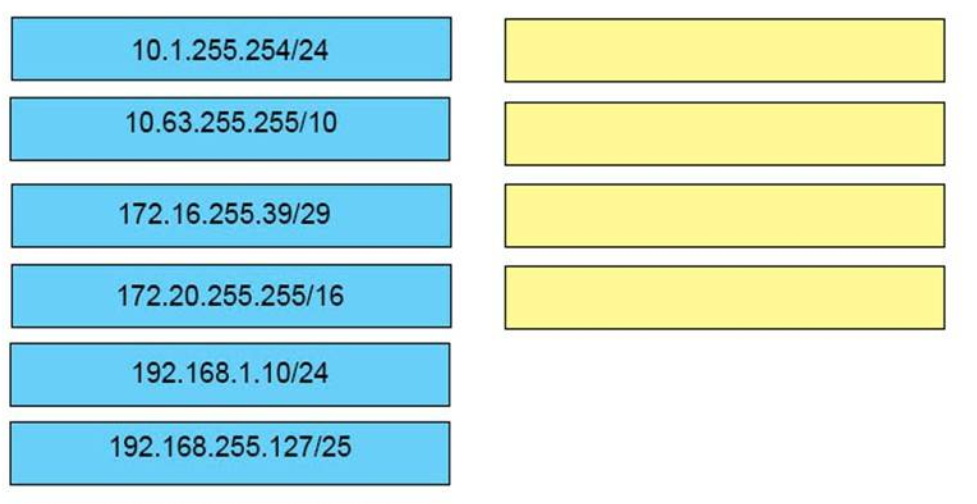
Right Reply:
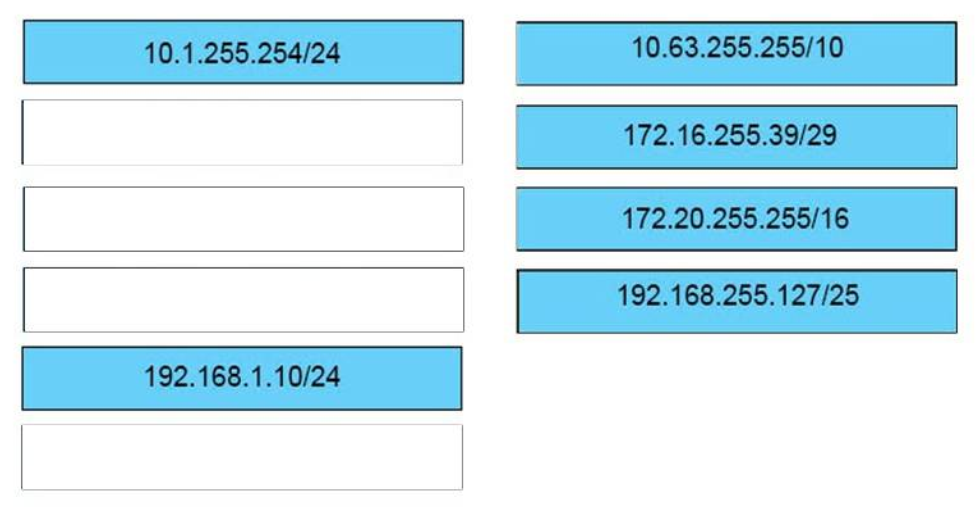
Answer:
10.63.255.255/10
172.16.255.39/29
172.twenty.255.255/sixteen
192.168.255.127/25
fourteen. DRAG Drop. Drag and Drop the descriptions of IP protocol transmissions from the left onto the correct IP traffic types on the correct.
Select and Place:
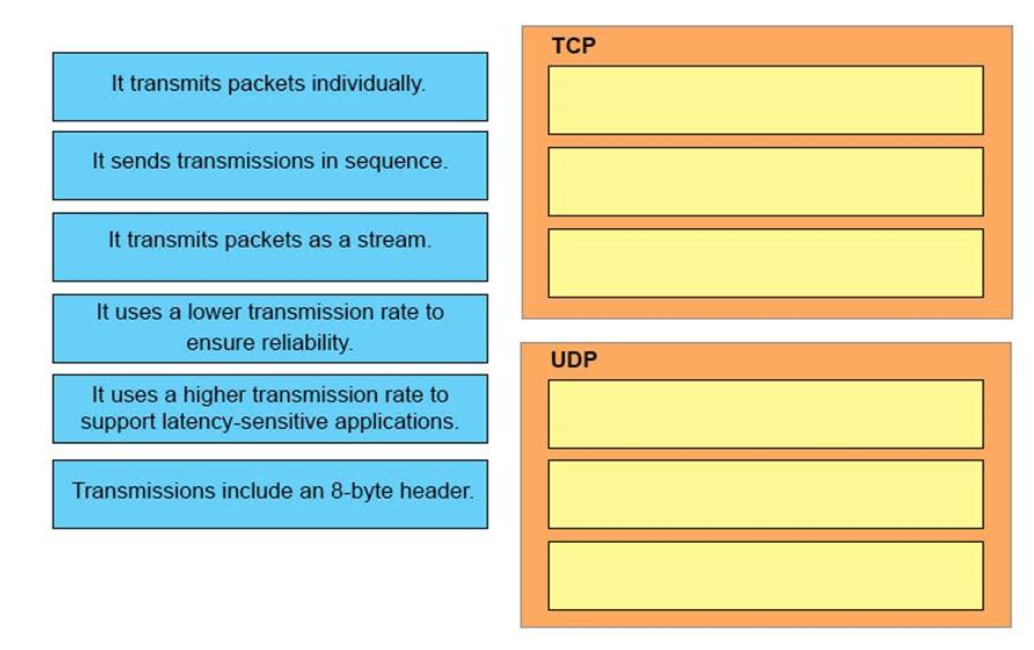
Correct Reply:
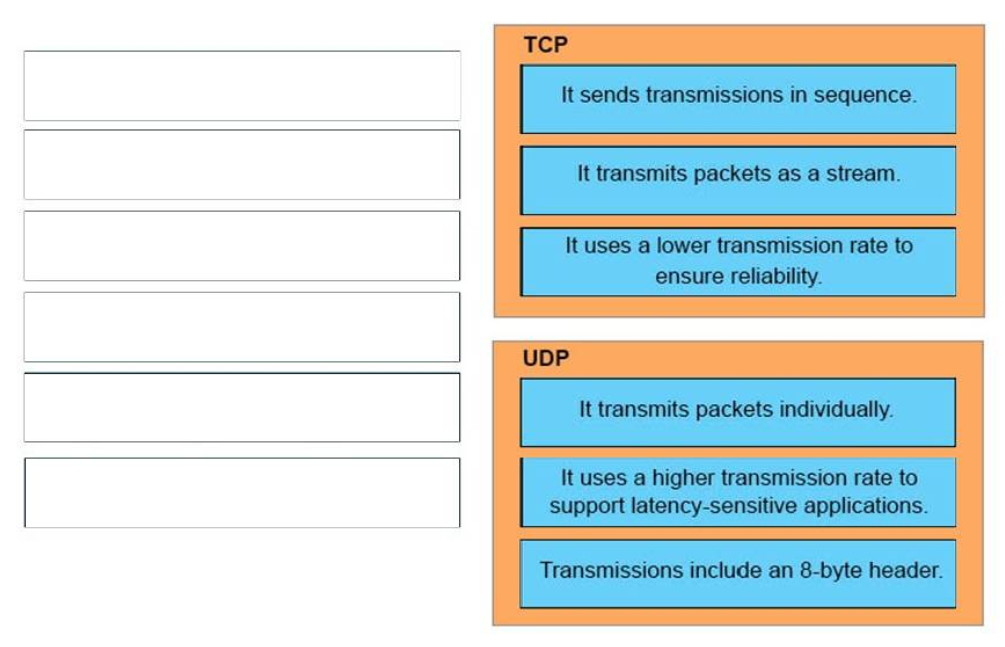
Answer:
TCP:
+ It sends transmissions in sequence.
+ It transmits packets as a stream.
+ It uses a lower transmission charge per unit to ensure reliability.
UDP:
+ Information technology transmits packets individually.
+ It uses a college transmission rate to support latency-sensitive applications.
+ Transmissions include an 8-byte header.
fifteen. Elevate DROP. Drag each category on the left to its respective router output line on the right. Each router output line is in the result of a bear witness ip interface command. Not all categories are used.
Select and Identify:
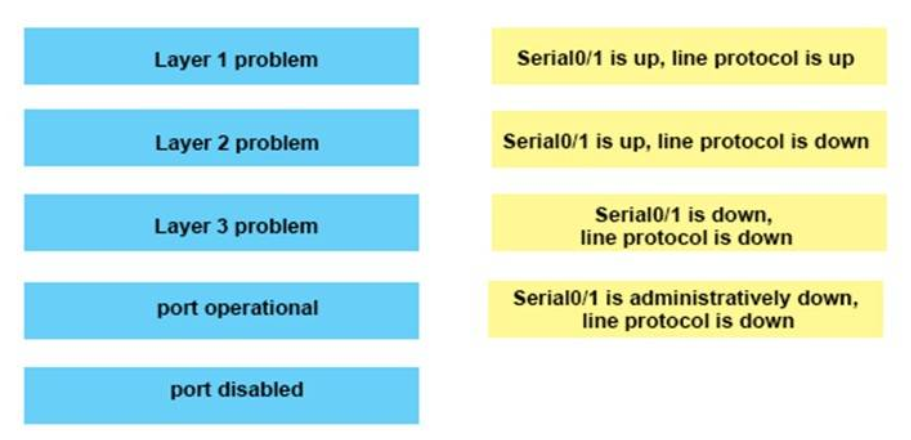
Correct Answer:
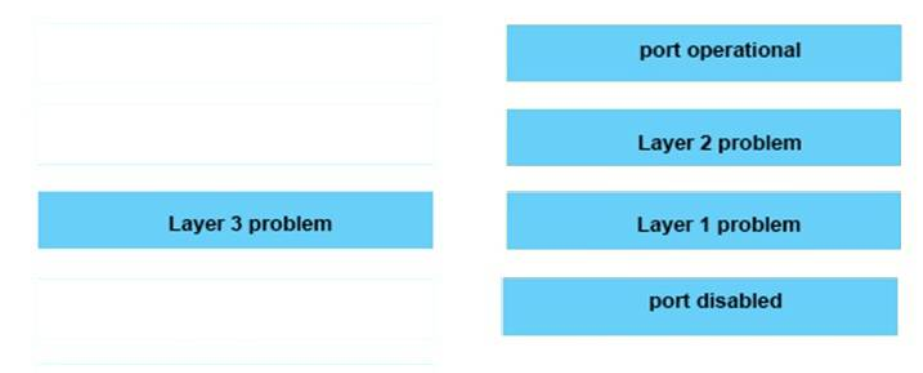
Answer:
Serial0/i is up, line protocol is upward : port operational
Serial0/i is up, line protocol is down : Layer 2 problem
Serial0/1 is down, line protocol is downward : Layer one problem
Serial0/1 is administratively down, line protocol is down : port disabled
16. Elevate DROP. Drag and driblet the networking features of functions from the left onto the planes on which they operate on the
right.
Select and Place:
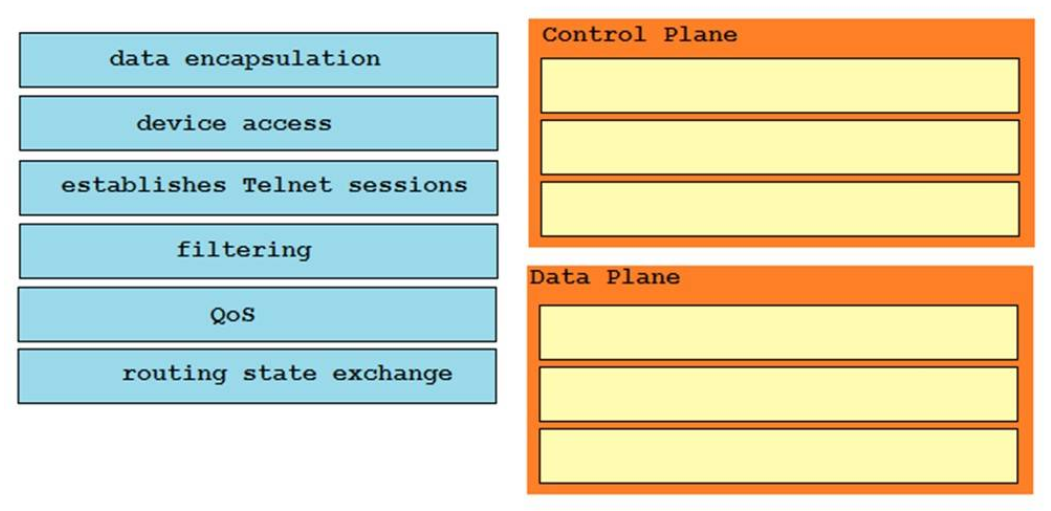
Correct Reply:
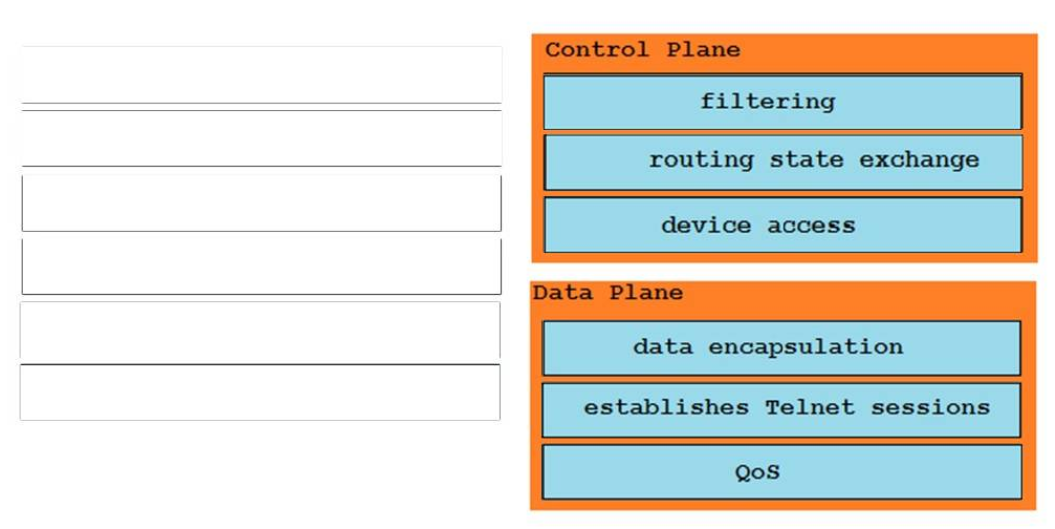
Answer:
Control Airplane:
Filtering
Routing state commutation
Device access
Data Airplane:
QoS
Establishes telnet session
Information Encapsulation
Show (Hide) Explanation/Reference
Thecontrol plane: The control aeroplane is the brain of the router. It consists of dynamic IP routing protocols (that is OSPF, IS-IS, BGP, and then on), the RIB, routing updates, in addition to other protocols such as PIM, IGMP, ICMP, ARP, BFD, LACP, and and so on. In short, the control plane is responsible for maintaining sessions and exchanging protocol information with other router or network devices.
Thedata aeroplane: The data plane is the forwarding aeroplane, which is responsible for the switching of packets through the router (that is, process switching and CEF switching). In the data plane, there could exist features that could affect packet forwarding such every bit quality of service (QoS) and access control lists (ACLs).
Reference: http://www.ciscopress.com/articles/article.asp?p=2272154&seqNum=iii
17. Elevate Drib. Y'all are connecting a variety of devices on your network. Drag and drop the combinations of devices from the left onto the correct cable types on the right.
Select and Identify:
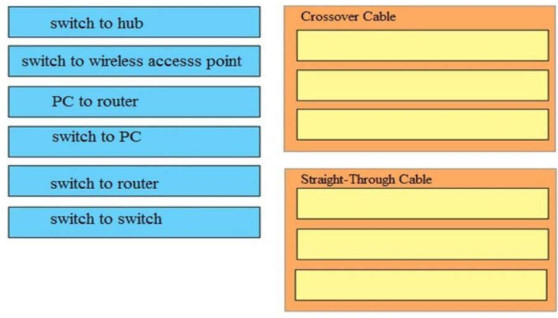
Answer:
Crossover Cable:
+ PC to router
+ switch to hub
+ switch to switch
Straight-Through Cable:
+ switch to PC
+ switch to router
+ switch to wireless accesss point
eighteen. Elevate DROP. Elevate and drop the STP features from the left onto the correct descriptions on the right.
Select and Place:
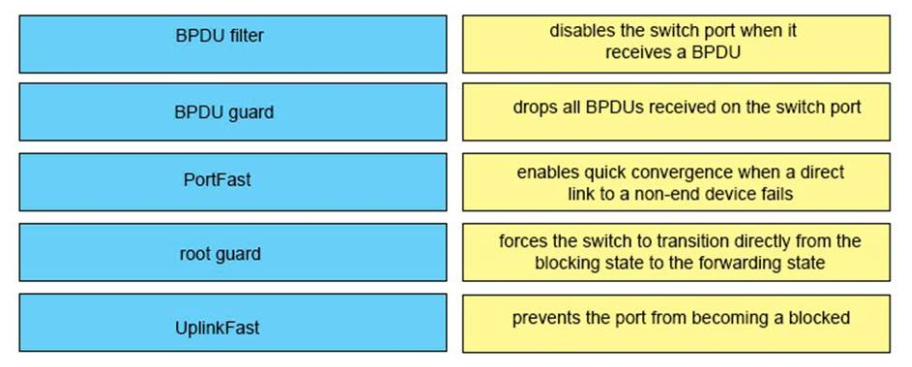
Correct Answer:
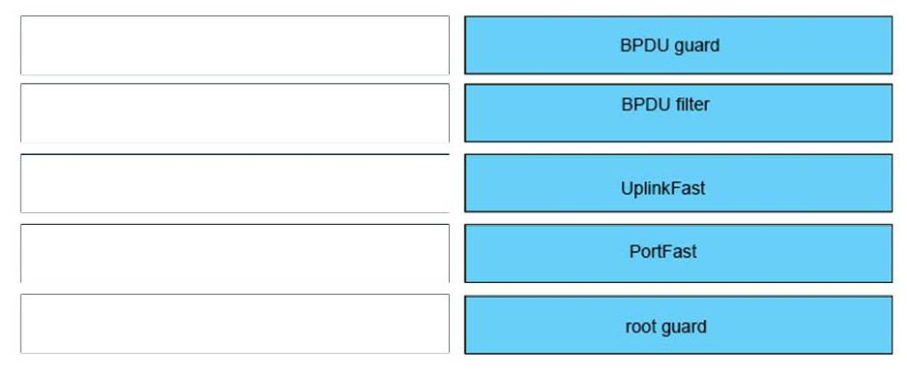
Reply:
+ BPDU Filter: drops all BPDU received on the switch port
+ BPDU guard: disables the switch port when it receives a BPDU
+ PortFast: forces the switch to transition straight from the blocking state to the forwarding state
+ Root guard: prevents the port from becoming a locked port
+ UplinkFast: enables quick convergence when a directly link to a non-end device fails
nineteen. Elevate DROP. Drag and drop the MAC accost types from the left onto the correct descriptions on the right?
Select and Identify:
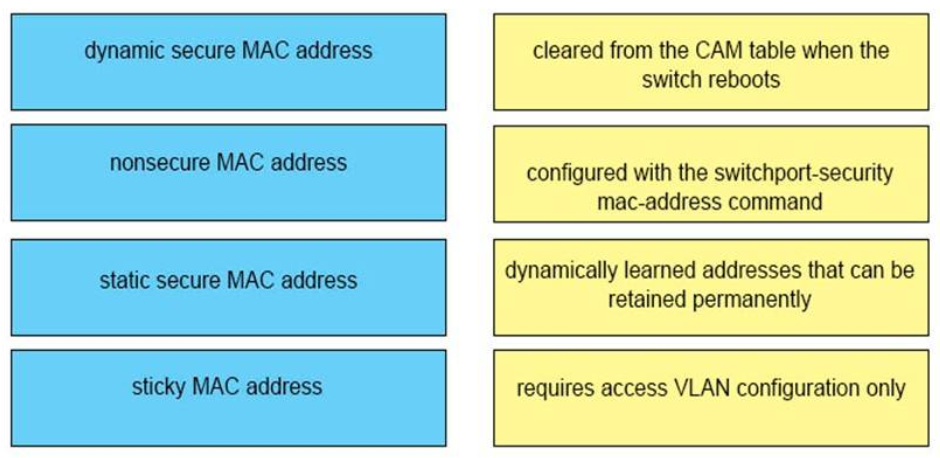
Correct Answer:
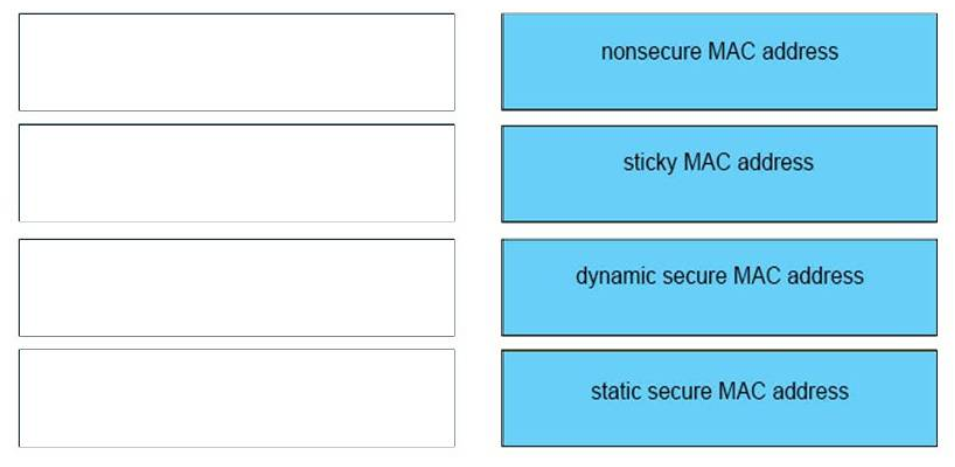
Answer:
– cleared from the CAM table when the switch reboots : nonsecure MAC address
– configured with the switchport-security mac-accost command : sticky MAC accost
– dynamically learned addresses that can be retained permanently : dynamic secure MAC address
– requires access VLAN configuration only : static secure MAC address
twenty. Elevate Drop. Drag and drop the BGP components from the left onto the right descriptions on the correct.
Select and Place:
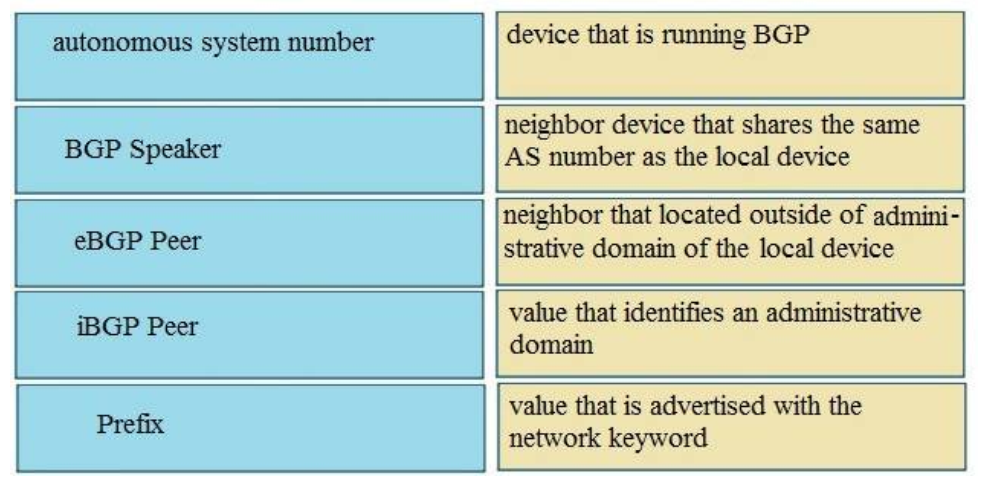
Right Answer:
Respond:
+ Device that running BGP:BGP speakers
+ Neighbor that share the aforementioned Every bit number as a local device:iBGP peer
+ Neighbour that located outside of AD domain of the local device:eBGP peer
+ Value that identify an Advertizing:Autonomous system number
+ Value that is advertise with network keyword:Prefix
21. DRAG Drib. Drag each definition on the left to the matching term on the right.
Select and Place:
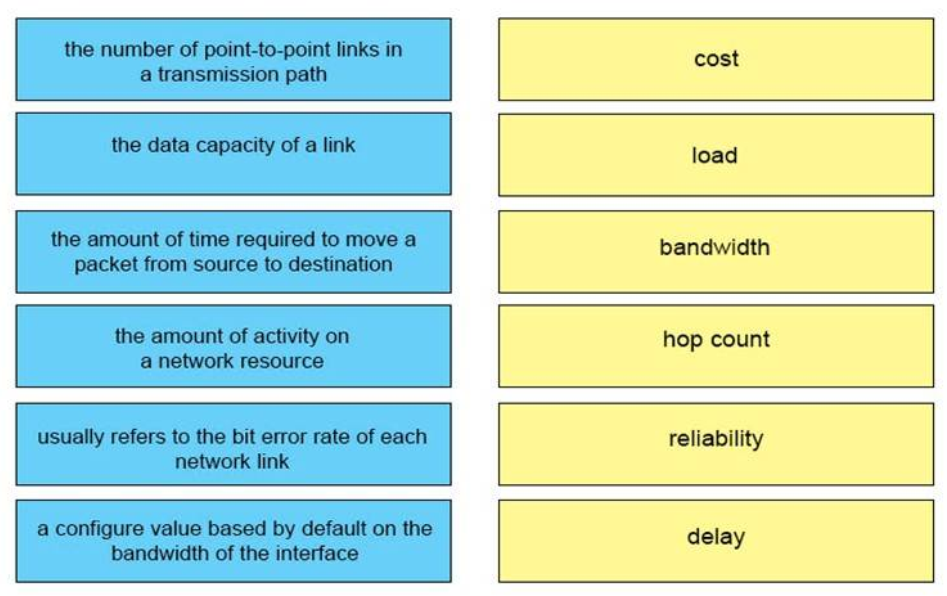
Correct Answer:
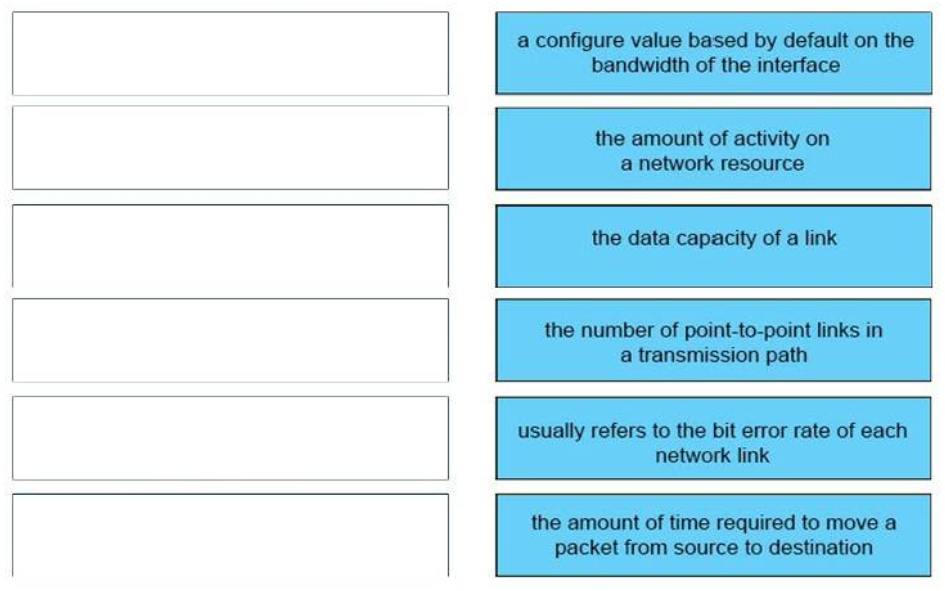
– price : a configure value based by default on the bandwidth of the interface
– load : the amount of action on a network resources
– bandwidth : the information capacity of a link
– hop count : the number of bespeak-to-betoken links in a manual path
– reliability : ordinarily refers to the fleck error rate of each network link
– delay : the amount of fourth dimension required to move a packet from source to destination
22. DRAG DROP. Drag the Cisco default administrative distance to the advisable routing protocol or route. (Not all options are
used.)
Select and Place:
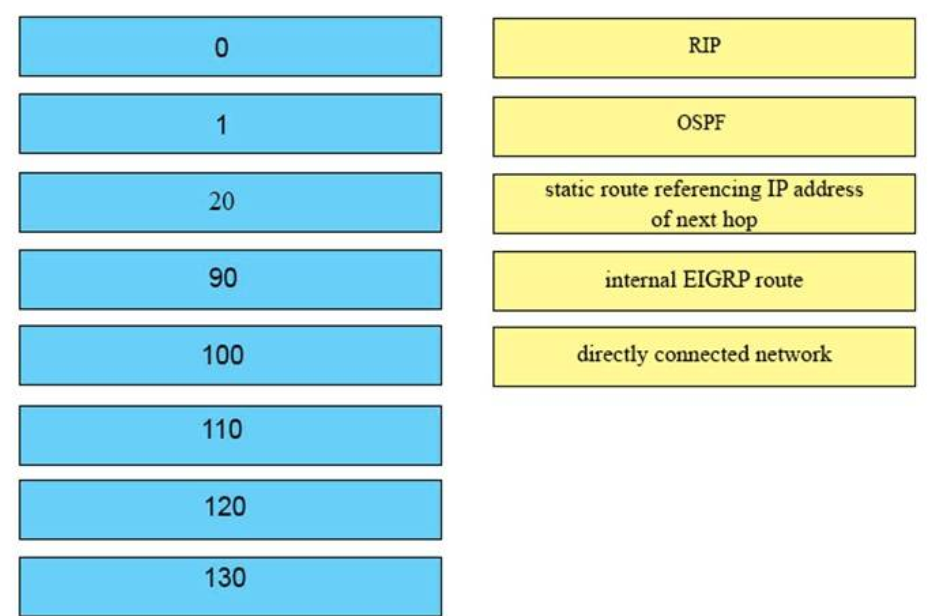
Correct Answer:
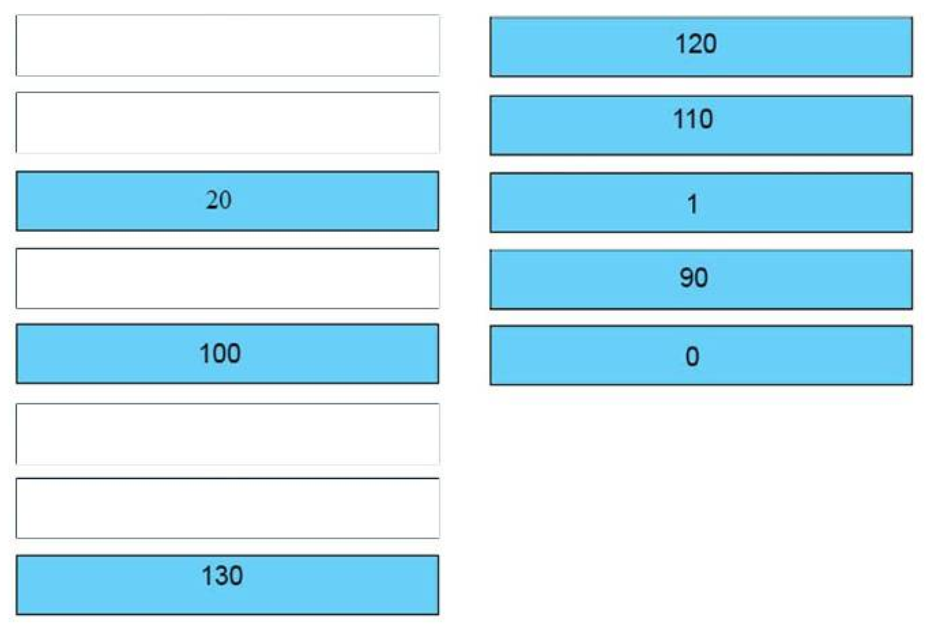
Respond:
+ RIP : 120
+ OSPF : 110
+ static route referencing IP address of side by side hop : 1
+ internal EIGRP road : 90
+ straight continued network : 0
23. DRAG Drop. Routing has been configured on the local router with these commands:
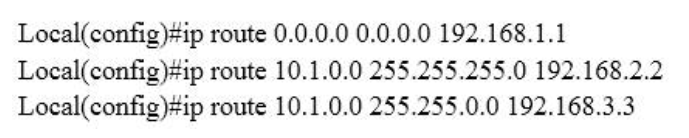
Drag each destination IP address on the left to its right next hop accost on the right.
Select and Identify:
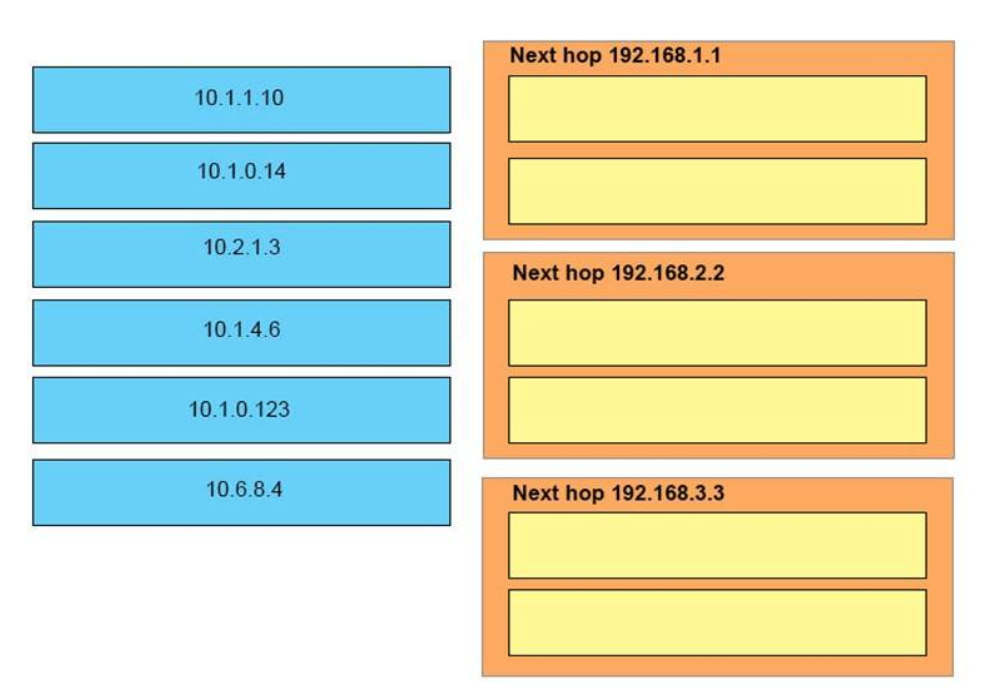
Correct Respond:
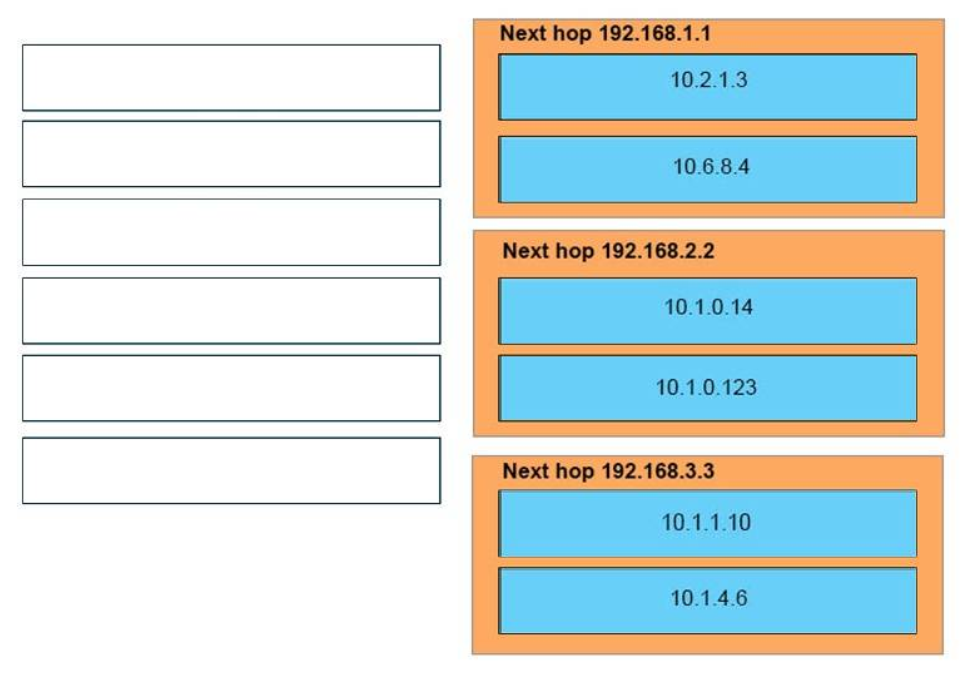
Answer:
Adjacent hop 192.168.one.1
10.2.ane.3
10.6.8.iv
Next hop 192.168.2.2
ten.one.0.14
10.1.0.123
Side by side hop 192.168.3.3
10.ane.one.ten
10.1.four.six
24. DRAG Driblet. Drag and drop each advantage of static or dynamic routing from the left onto the correct routing blazon on the right. Select and Place:
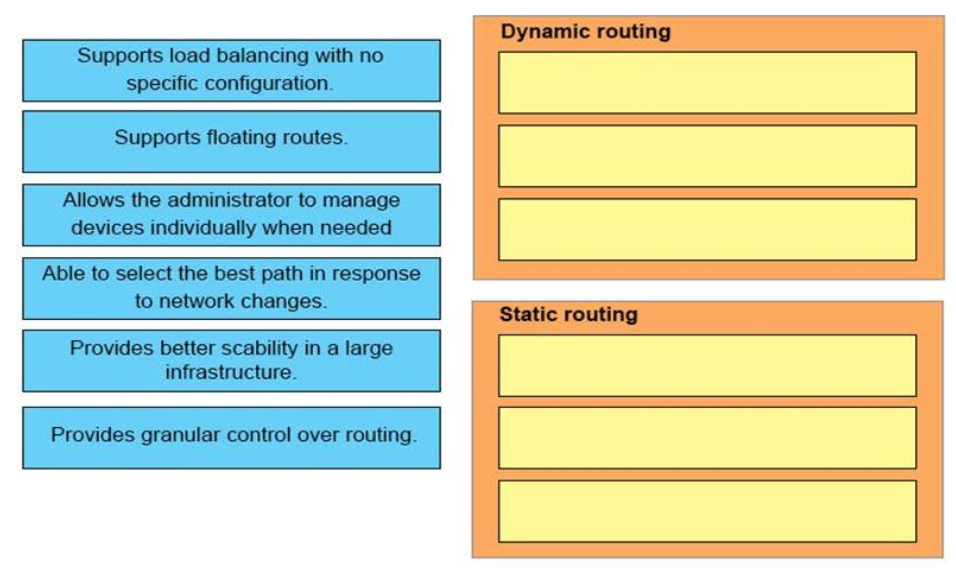 Correct Answer:
Correct Answer:
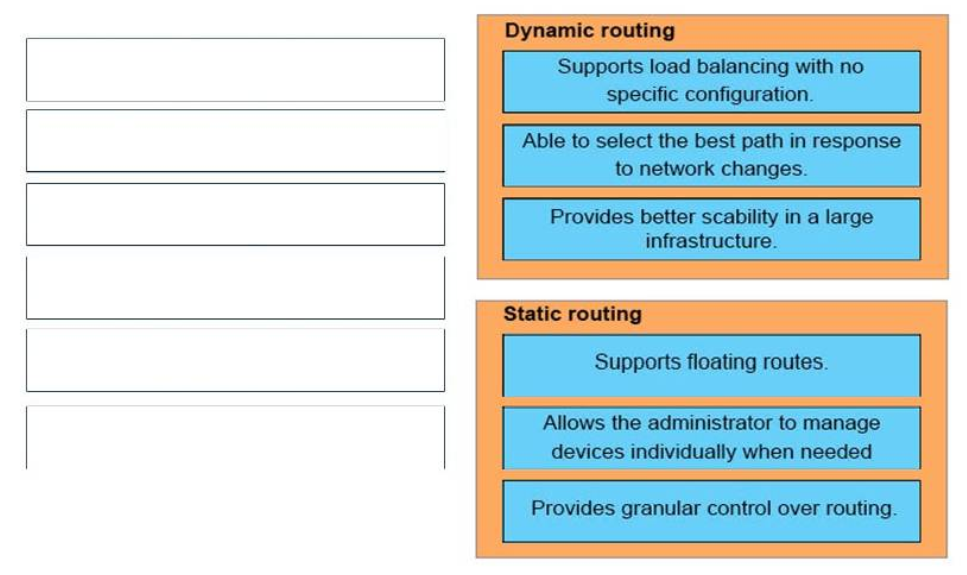
Reply:
Static Routing:
+ Allows the ambassador to manage devices individually when needed
+ Supports floating routes
+ Provides granular control over routing
Dynamic Routing:
+ Able to select the best path in response to network changes
+ Supports load balancing with no specific configuration
+ Provides better scalability in a large infrastructure
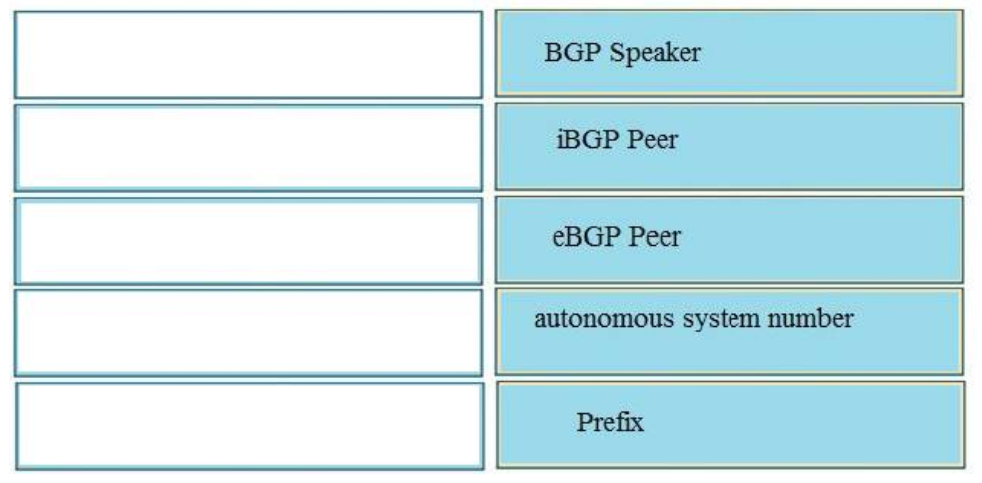
25. Elevate Drop. Drag and driblet the BGP terms from the left onto the correct descriptions on the correct. Select and Place:
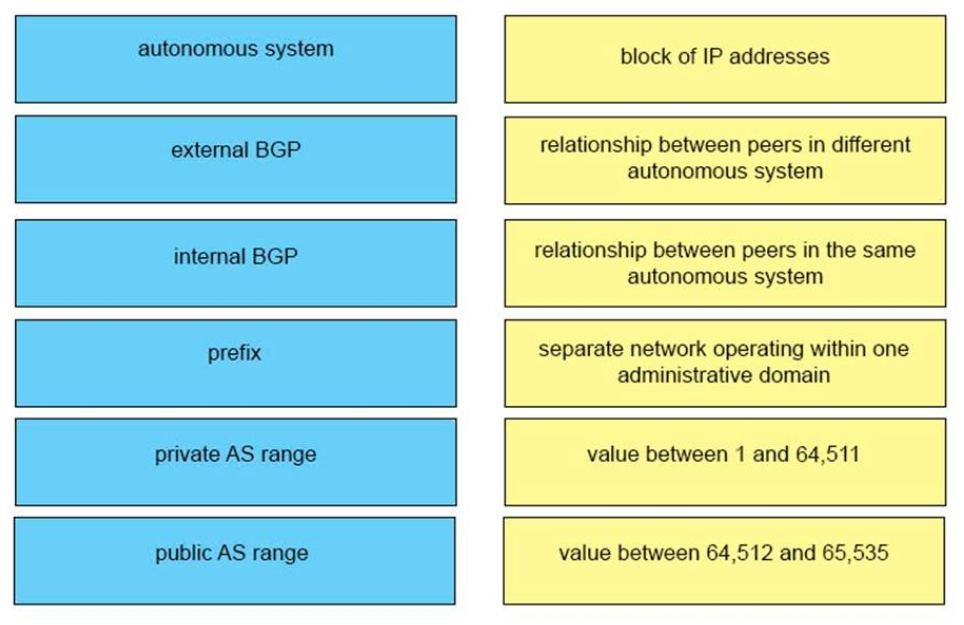 Correct Answer:
Correct Answer:
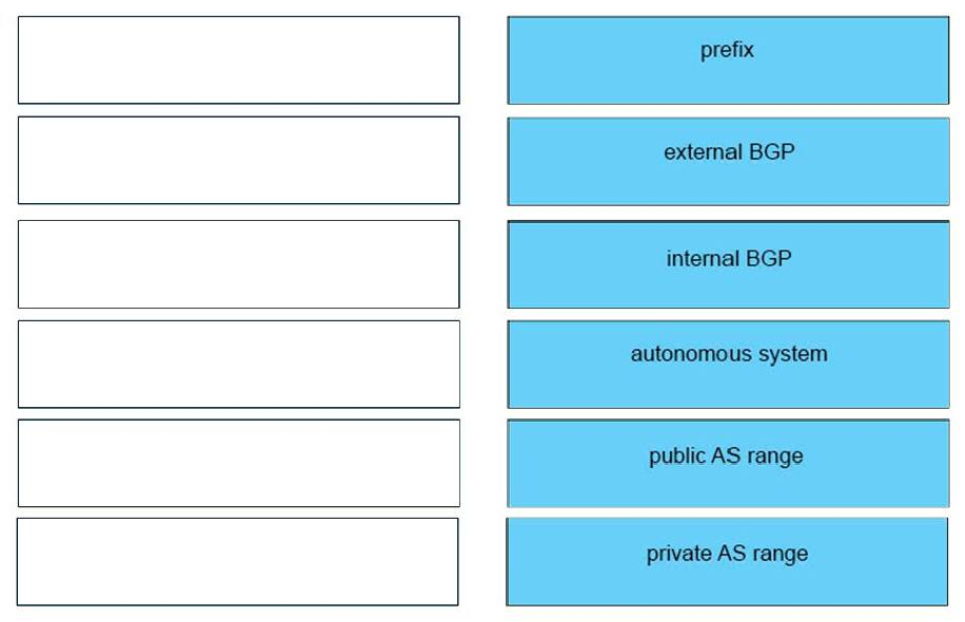
Respond:
iBGP <-> relationship between peers in aforementioned autonomous organization
eBGP <-> relationship between peers in unlike autonomous system
Prefix <-> cake of IP addresses
Private Every bit range <-> Value between 64,512 and 65,535
Public Equally range <-> Value between 1 and 64,511
Autonomous System <-> separate network operating within 1 administrative domain
26. DRAG Drop. Drag and drop the values in a routing table from the left onto the correct meanings on the right. Select and Place:
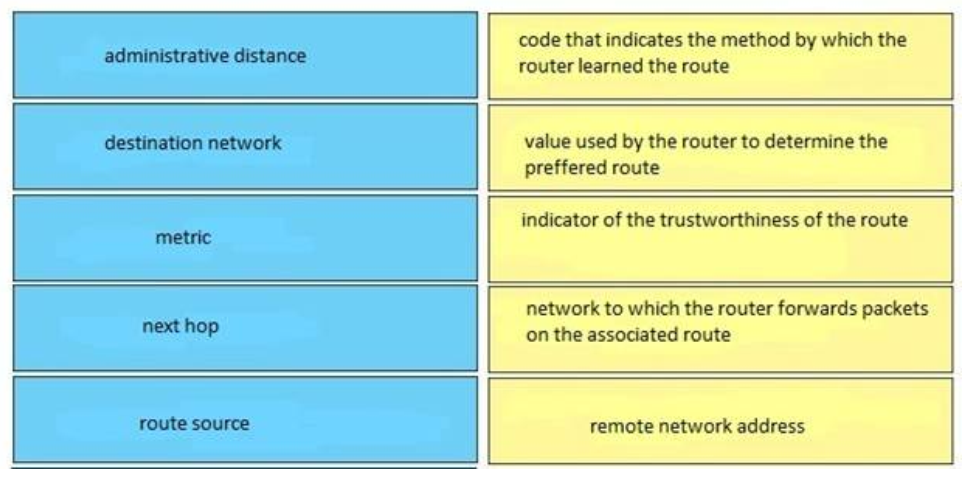
Correct Respond:
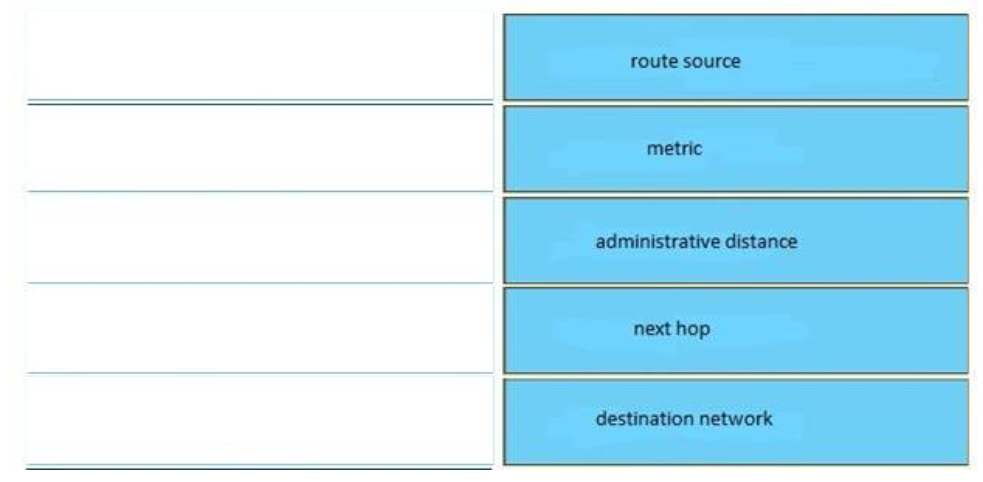
Answer:
+ Authoritative distance: indicator of the trustworthiness of the route
+ Destination network: remote network address
+ Metric: value used by the router to determine the preferred route
+ Next hop: network to which the router forwards packets on the associated route
+ Road source: code that indicates the method by which the router learned the road
27. DRAG DROP. Drag the frame relay acronym on the left to friction match its definition on the correct. (Not all acronyms are used.) Select and Identify:
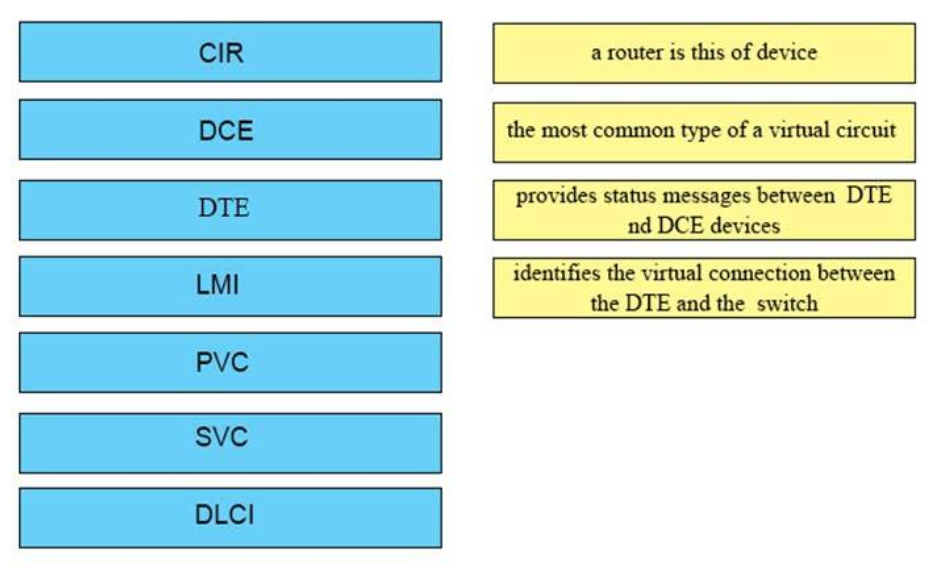 Correct Answer:
Correct Answer:
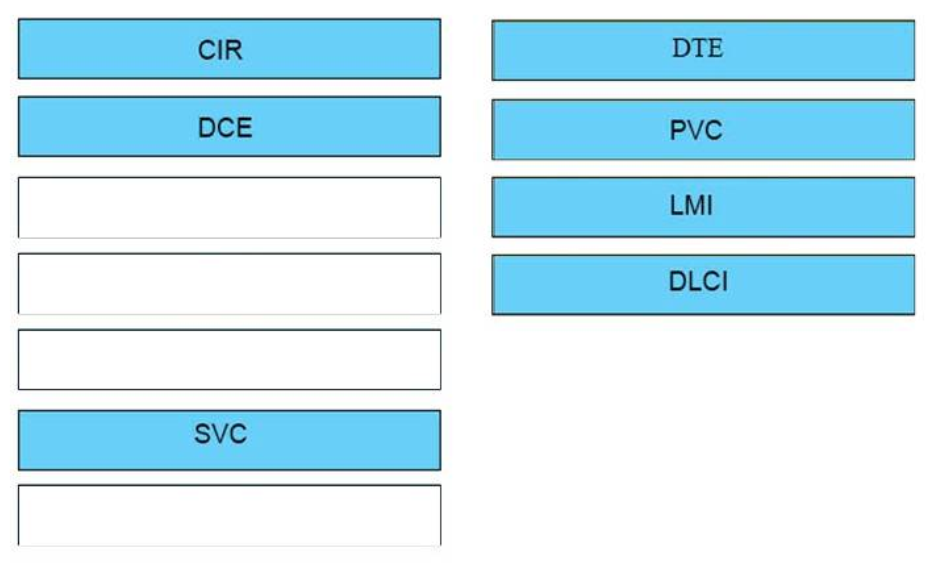
Answer:
a router is this of device <-> DTE
the most common blazon of a virtual circuit <-> PVC
provides status messages between DTE nd DCE devices <-> LMI
identifies the virtual connexion between the DTE and the switch <-> DLCI
28. Drag Drib. Drag and drib the QoS features from the left onto the right descriptions on the correct. Select and Identify:
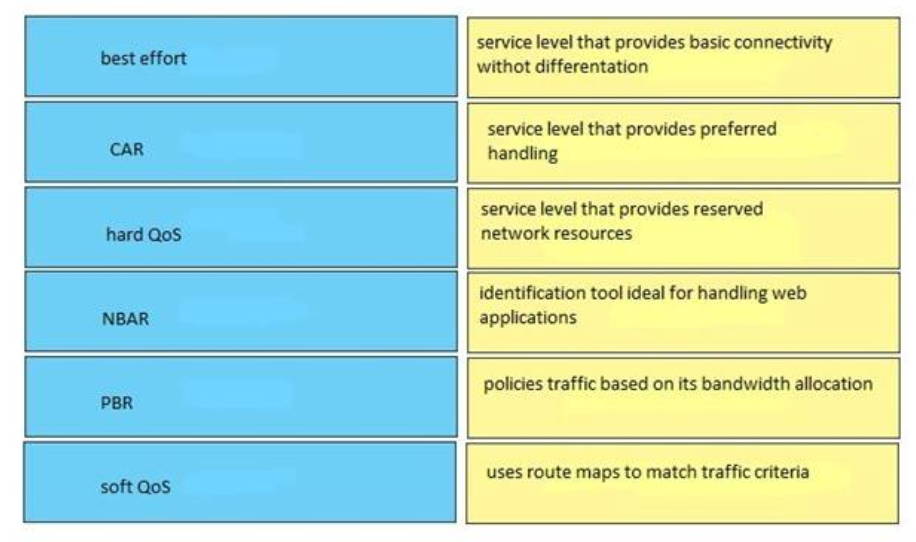 Correct Reply:
Correct Reply:
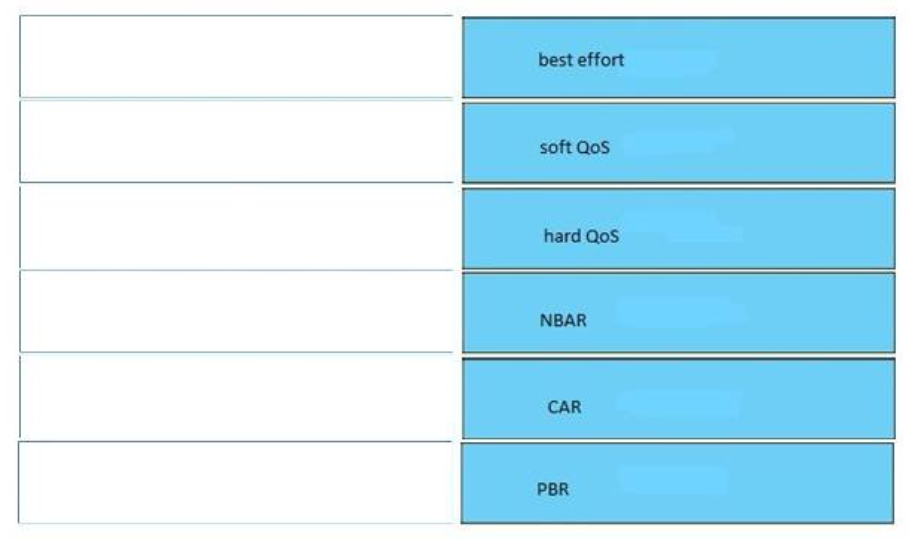
Answer:
+ Automobile: policies traffic based on its bandwidth allocation
+ Best endeavour: service level that provides basic connectivity without differentiation
+ Soft QoS: service level that provides preferred handling
+ Difficult QoS: service level that provides reserved network resources
+ PBR: uses road maps to match traffic criteria
+ NBAR: identification tool ideal for treatment web applications
Note:
+ Committed Access Rate (CAR)
+ Network-based application recognition (NBAR)
+ Policy-based routing (PBR)
+ Soft QoS: also known as Differentiated Services (Diffserv), which ensures resources for
applications based on available bandwidth
+ Difficult QoS: Differentiated Service (DiffServ) is an appropriate instance for this type of QoS service
29. Elevate DROP. Drag and drop the PPPoE message types from the left into the sequence in which PPPoE letters are sent on the right. Select and Place:
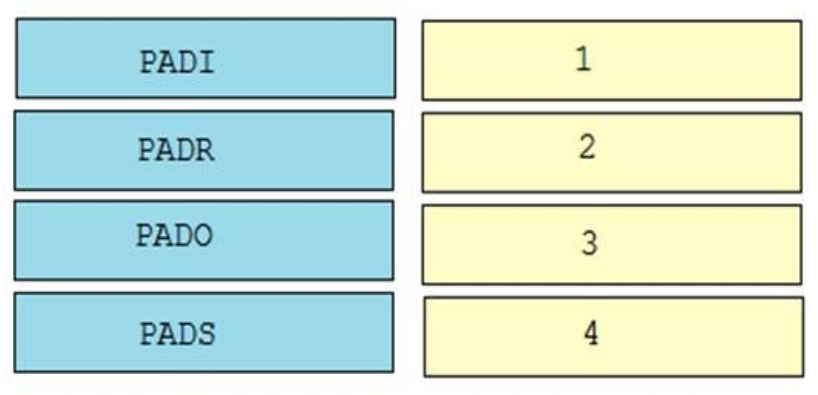 Correct Answer:
Correct Answer:
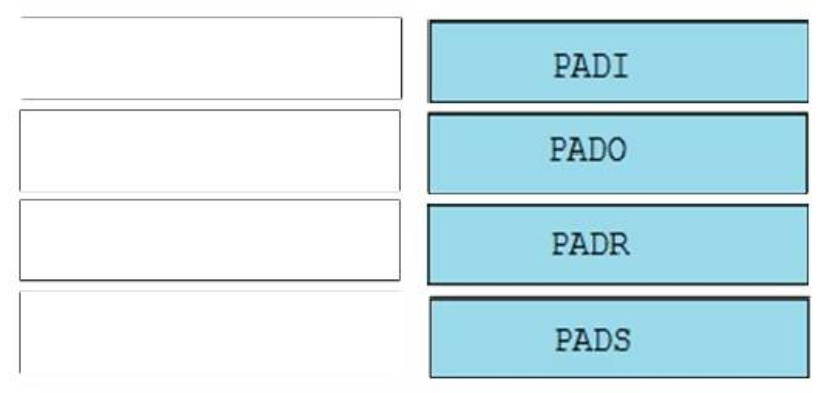
Answer:
ane. PADI
2. PADO
3. PADR
4. PADS
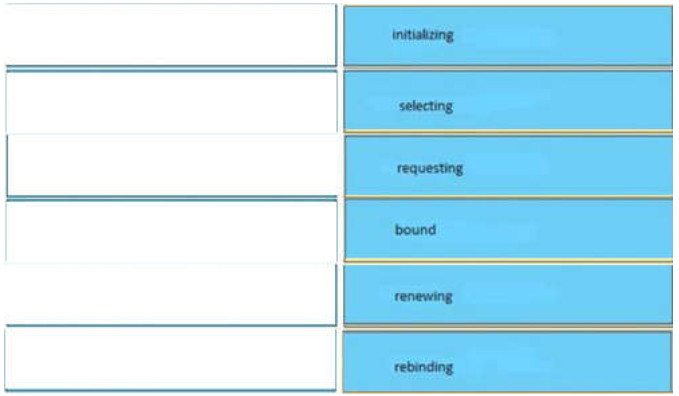
30. Elevate Drib. Drag and drop the DHCP customer states from the left into the standard order in which the client passes through
them on the right.
Select and Identify:
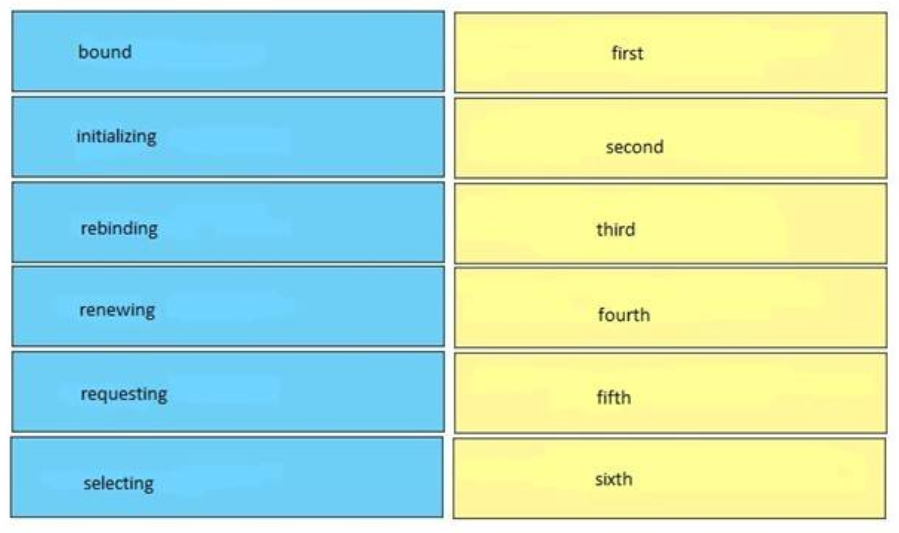
Correct Answer:
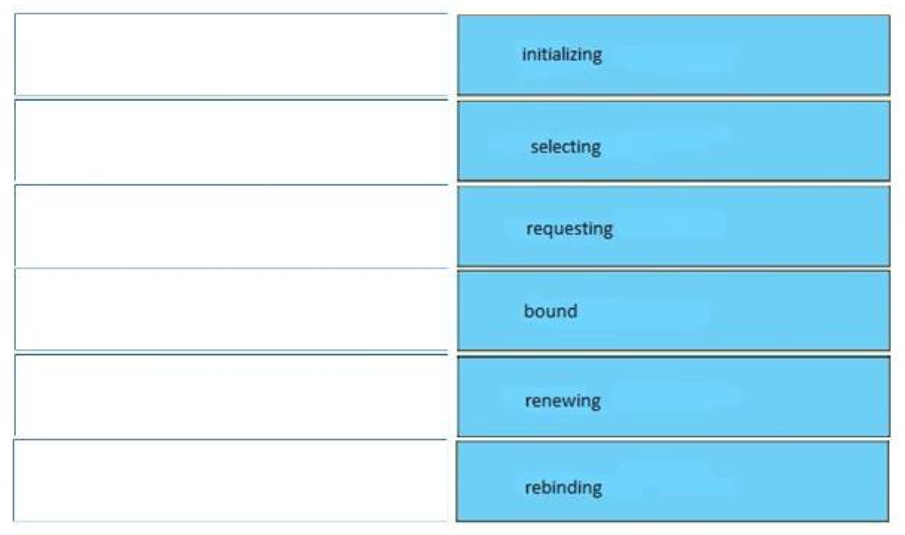
Answer:
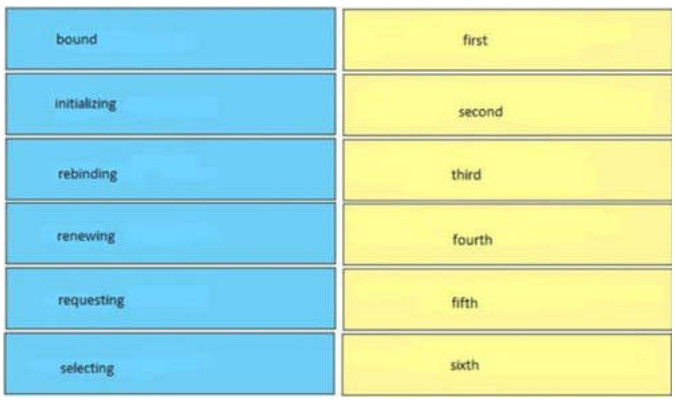
initializing – kickoff
selecting – second
requesting – third
spring – fourth
renewing – fifth
rebinding – 6th
31. DRAG DROP. Drag and drop the DNS lookup commands from the left onto the right effects on the correct.
Select and Identify:
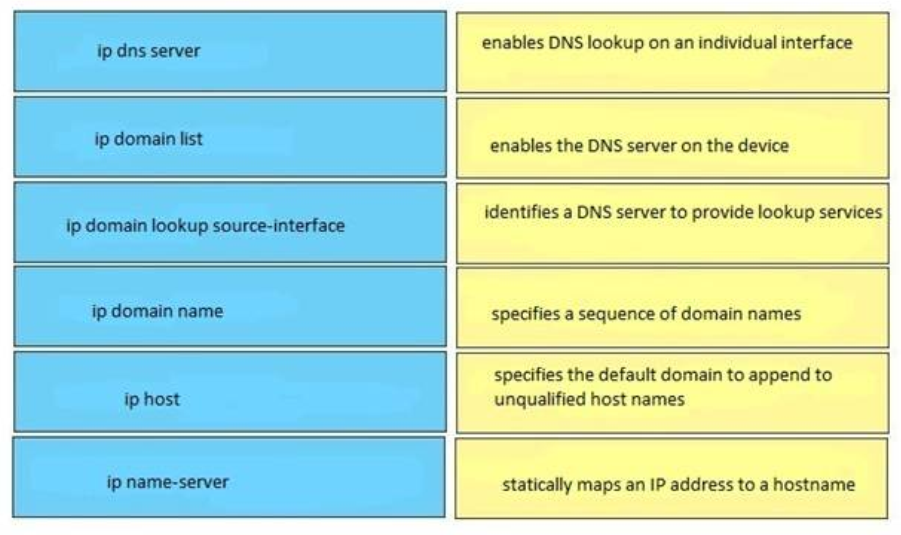
Correct Reply:
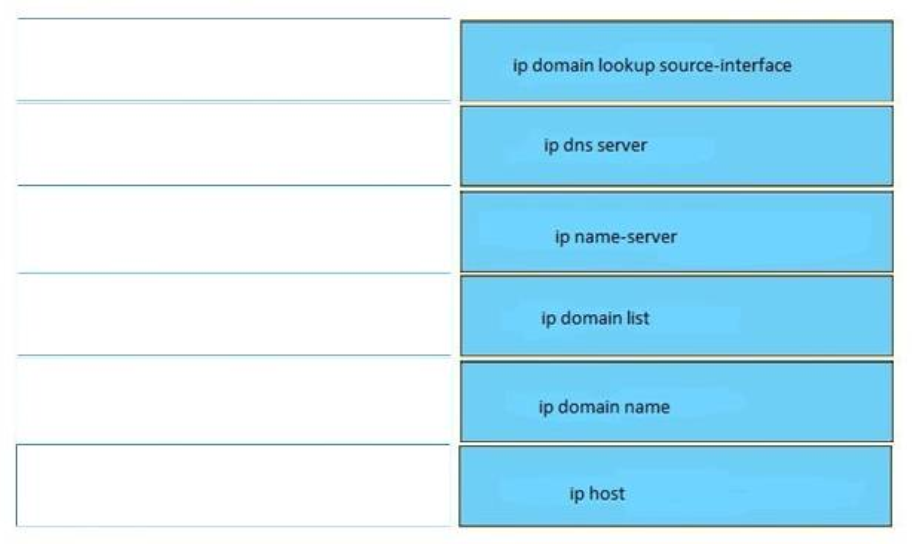
Respond:
enables DNS lookup on an private interface <-> ip domain lookup source-interface
enables the DNS server on the device <-> ip dns server
identifies a DNS server to provide lookup services <-> ip name-server
specifies a sequence of domain names <-> ip domain list
specifies the default domain to append to unqualified host names <-> ip domain proper name
statically maps an IP address to a hostname <-> ip host
Show (Hibernate) Explanation/Reference
32. Drag DROP. Drag and drop the protocols from the left onto the right IP traffic types on the right.
Select and Place:
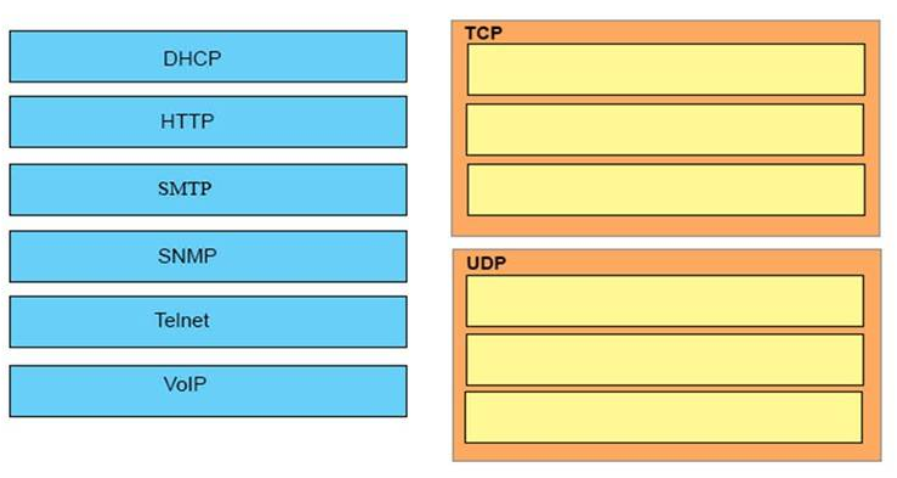
Correct Answer:
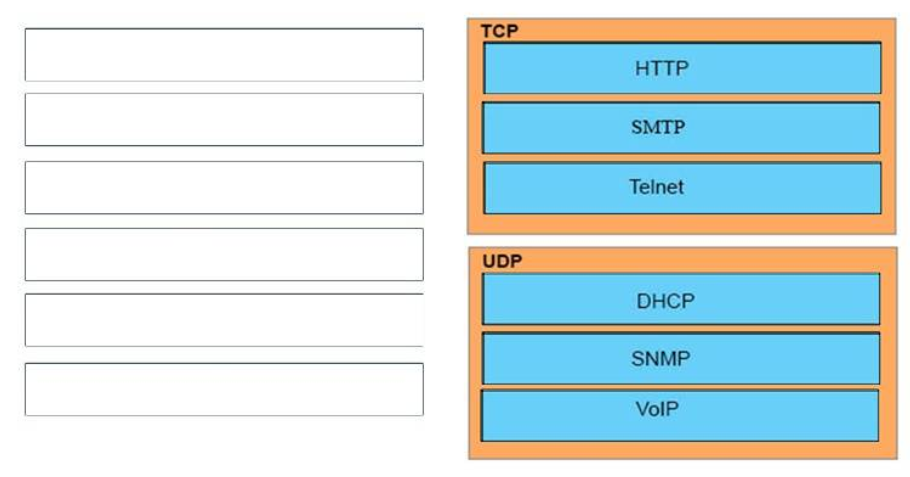
Reply:
TCP:
+ HTTP
+ SMTP
+ Telnet
UDP:
+ DHCP
+ SNMP
+ VoIP
33. DRAG Drop. Order the DHCP message types as they would occur between a DHCP client and a DHCP server.
Select and Place:
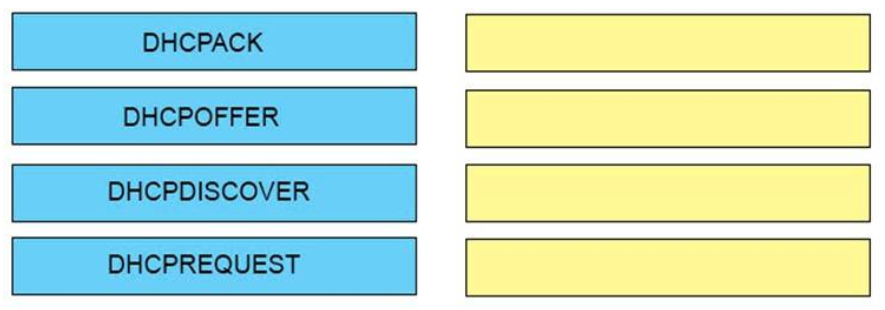
Right Answer:
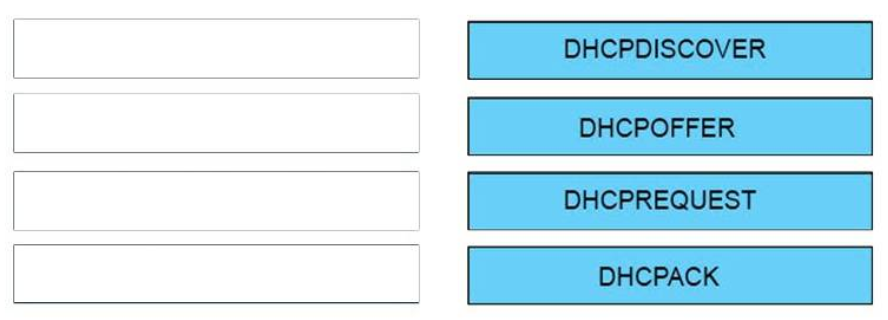
Respond:
DHCPDISCOVER
DHCPOFFER
DHCPREQUEST
DHCPACK
34. DRAG DROP. Drag the security features on the left to the specific security risks they aid protect against on the right. (Not all options are used.)
Select and Place:
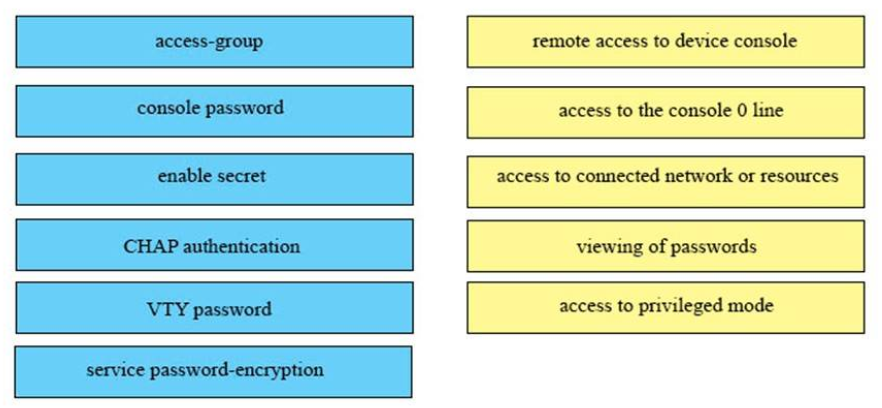
Correct Reply:
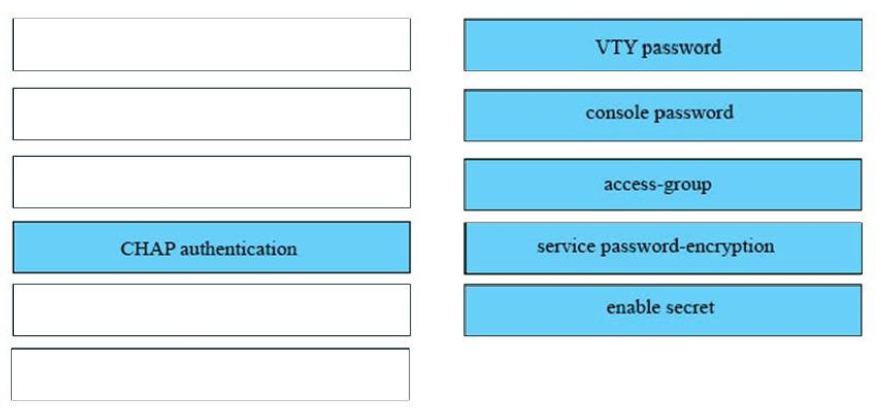
Answer:
1) VTY password: remote access to device console
two) console password: access to the panel 0 line
three) access-group: access to connected networks or resources
4) service password-encryption: viewing of passwords
5) enable secret: admission to privileged mode
The unselected left-box – CHAP – is used to verify the identity of the peer by ways of a 3-style handshake.
35. DRAG DROP. An interface has been configured with the access list that is shown below. On the basis of that admission listing,elevate each information package on the left to the appropriate category on the right.
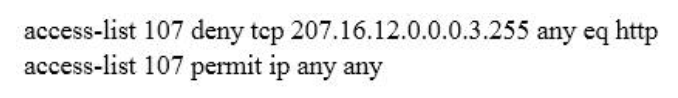
Select and Place:
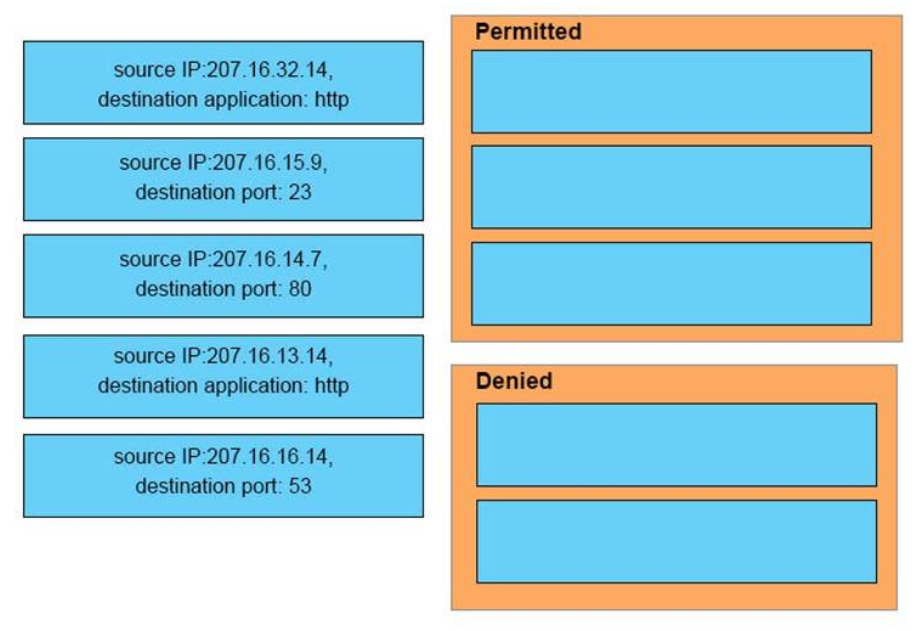
Correct Answer:
Reply:
Permitted
– source IP:207.xvi.32.14, destination application: http
– source IP:207.16.15.9, destination port: 23
– source IP:207.16.sixteen.14, destination port: 53
Denied
– source IP:207.16.14.7, destination port: 80
– source IP:207.16.13.14, destination application: http
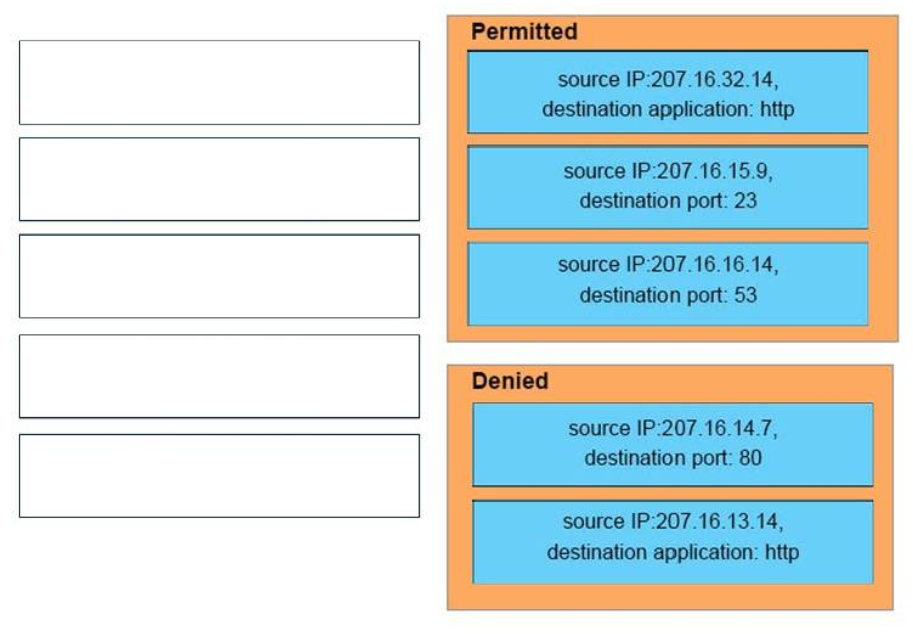
36. DRAG Drop. Elevate and drop the extended traceroute options from the left onto the correct descriptions on the correct.
Select and Place:
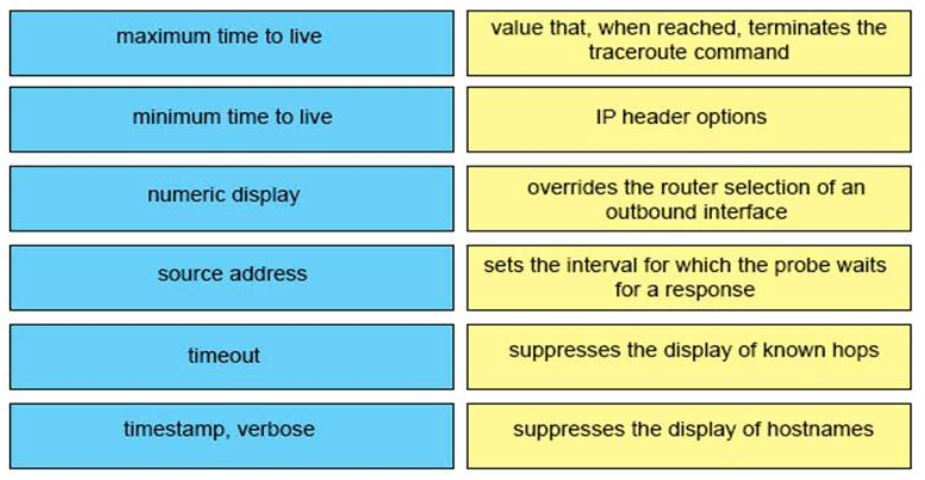
Correct Answer:
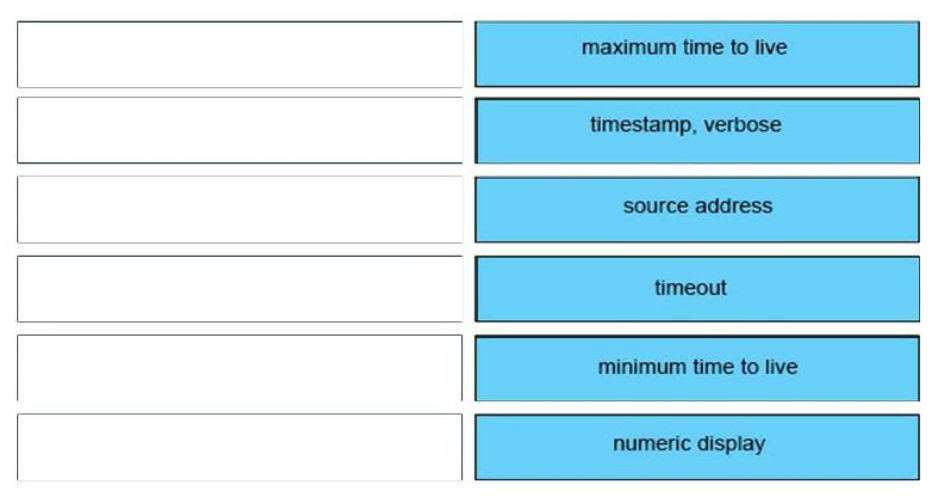
Answer:
+ Maximum time to live: value that, when reached, terminates the traceroute command
+ Minimum time to live: suppresses the display of known hops
+ Numeric display: suppresses the display of hostnames
+ Source address: overrides the router choice of an outbound interface
+ Timeout: sets the interval for which the probe waits for a response
+ Timestamp, verbose: IP header options
Show (Hide) Explanation/Reference
37. DRAG DROP. Elevate and drop the descriptions of performing an initial device configuration from the left onto the correct features or components on the right.
Select and Place:
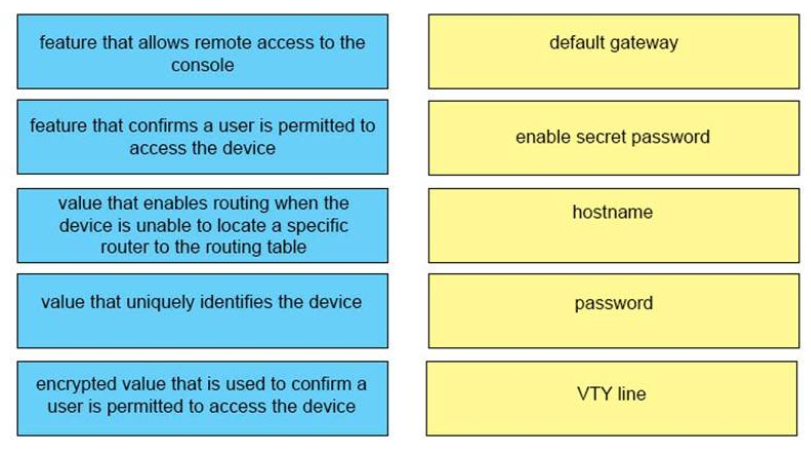
Right Answer:
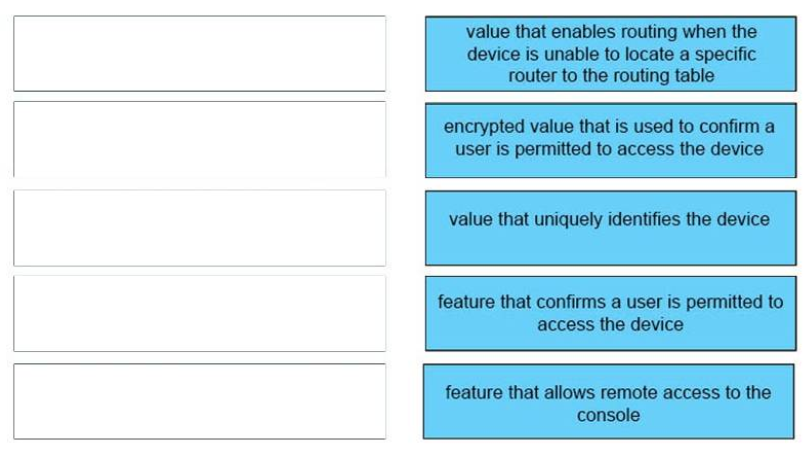
Respond:
default gateway <-> value that enables routing when the device is unable to locate a specific router to the routing tabular array
enable clandestine password <-> encrypted value that is used to confirm a user is permitted to access the device
hostname <-> value that uniquely identifies the device
password <-> feature that confirms a user is permitted to access the device
VTY line <-> feature that allows remote access to the console
38. Drag DROP. Drag and drop the descriptions of logging from the left onto the right logging features or components on the correct.
Select and Identify:
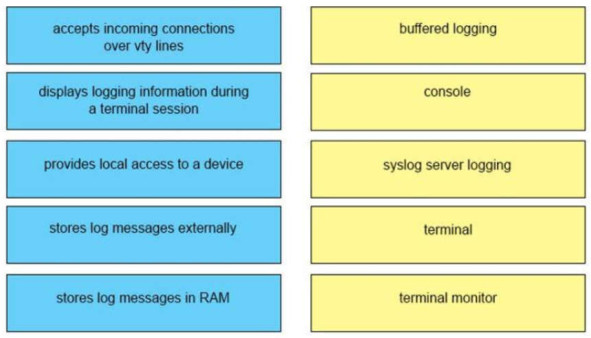
Reply:
buffered logging <-> stores log messages in RAM
panel <-> provides local admission to a device
syslog server logging <-> stores log messages externally
terminal <-> accepts incoming connections over vty lines
terminal monitor <-> displays logging information during a last session
39. DRAG Drop. Y'all are performing the initial configuration on a new Cisco device. Drag the job from the left onto the required or optional category on the right.
Select and Identify:
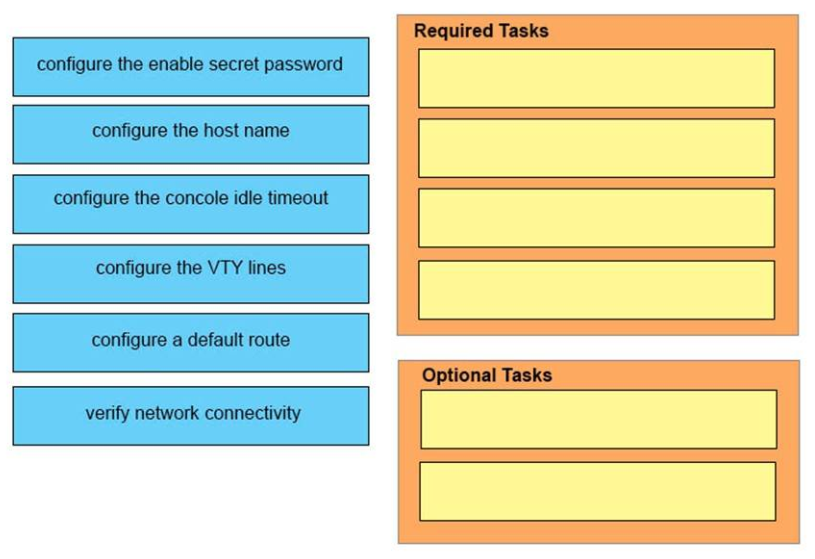
Correct Answer:
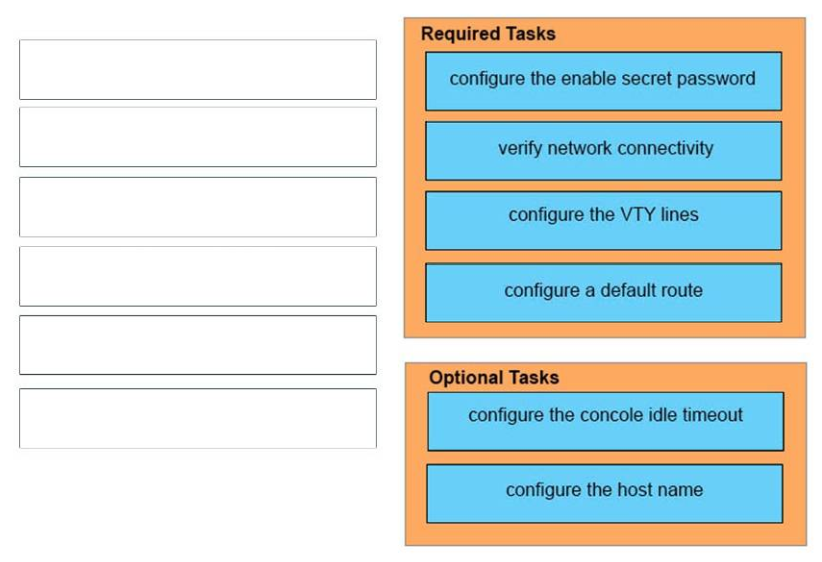
Required Tasks :
+ configure the enable secret password
+ verify network connectivity
+ configure the VTY lines
+ configure a default route
Optional Tasks :
+ configure the concole idle timeout
+ configure the host name
Show (Hide) Explanation/Reference
https://www.cisco.com/c/en/united states of america/td/docs/routers/access/2900/hardware/installation/guide/
Hardware_Installation_Guide/Configure.html#91811
twoscore. DRAG DROP. Drag and driblet the network programmability features from the left onto the right description on the right.
Select and Place:
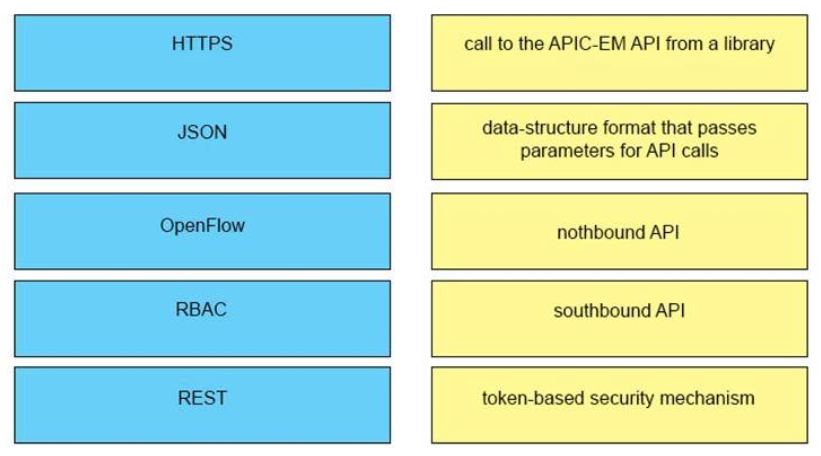
Correct Respond:

Answer:
+ HTTPS: token-based security machinery
+ JSON: data-structure format that passes parameters for API calls
+ OpenFlow: southbound API
+ RBAC: phone call to the APIC-EM API from a library
+ Residue: northbound API
Show (Hide) Explanation/Reference
What is the data format used to send/receive data when making REST calls for APIC-EM?
Javascript Object Notation (JSON) is used to pass parameters when making API calls and is too the returned data format.
What'southward RBAC?
The Role-Based Access Controls (RBAC) mechanism utilizes security tokens that the controller issues upon successful authentication of a user of the APIC-EM controller. All subsequent requests from the authenticated user must provide a valid token.
Reference: https://communities.cisco.com/docs/DOC-60530#q16
41. Elevate DROP. Drag and drib each WAN pattern pick on the left onto the correct clarification on the right.
Select and Place:
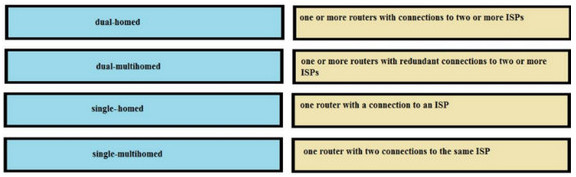
Correct Answer:
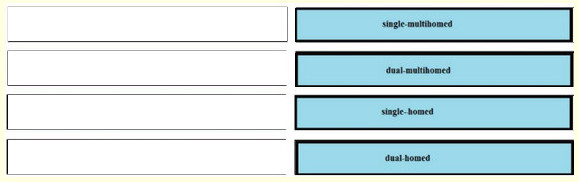
Respond:
one or more routers with connections to two or more ISPs <-> single-multihomed
one or more routers with redundant connections to two or more ISPs <-> dual-multihomed
ane router with a connection to an Isp <-> single-homed
one router with two connections to the same Internet access provider <-> dual-homed
42. Elevate DROP.
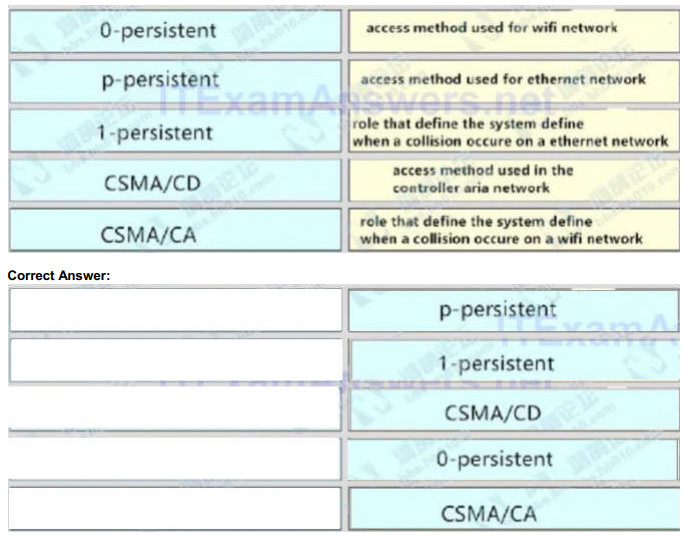
access method used for wifi network <-> p-persistent
access method used for ethernet network <-> 1-persistent
role that ascertain the system define when a collision occure on a ethernet network <-> CSMA/CD
access method used in the controller aria network <-> 0-persistent
role that define the system define when a collision occure on a wifi network <-> CSMA/CA
44. Elevate and drop the awarding protocols from the left onto the transport protocols that is uses on the right.
Right Answer:
45.
Right Answer:
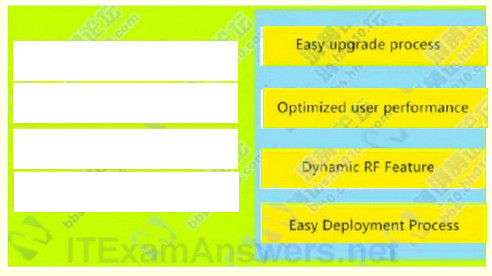
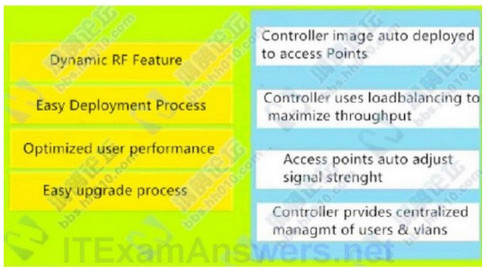
Controller image auto deployed to access Points : Like shooting fish in a barrel upgrade procedure
Controller uses loadbalancing to maximize throughput : Optimized user operation
Admission points auto adapt signal strenght : Dynamic RF Feature
Controller prvides centralized managmt of users & vlans : Easy Deployment Process
46.
Right Answer:

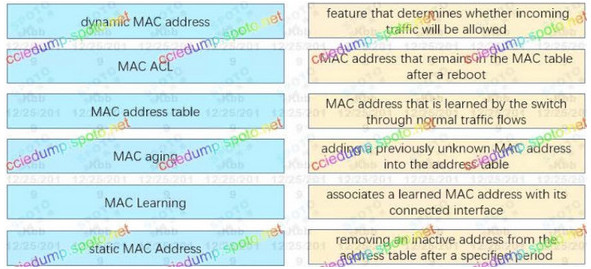
mac address that is learned past the switch through normal traffic flows : Dynamic mac address
associates a learned mac accost with its continued interface : Mac address tabular array
removing an inactive mac after a specified fourth dimension : Mac aging
characteristic that determines whether incoming traffic will exist allowed : Mac ACL
adding a previously unknown mac into the address table : Mac learning
mac address that remains in the mac address tabular array after reboot : Static mac
47.
Correct Answer:
– Discover to server : initializing
– from Offering from server : selecting
– Request to server : requesting
– from Ack from server : bound
– from same dhcp server : renewing
– from different dhcp server : rebinding
48.
RIPV1 :
– classful
– Non support authentication
Updates send in broadcast
– Non back up VLSM
RIPV2:
– ciassiess
– support authentication
– Updates ship in multicast
– Support VLSM
49.
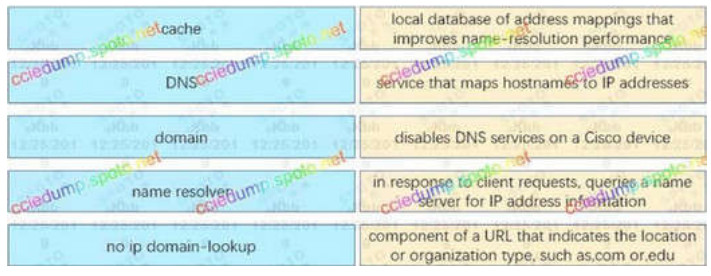
Correct Respond:
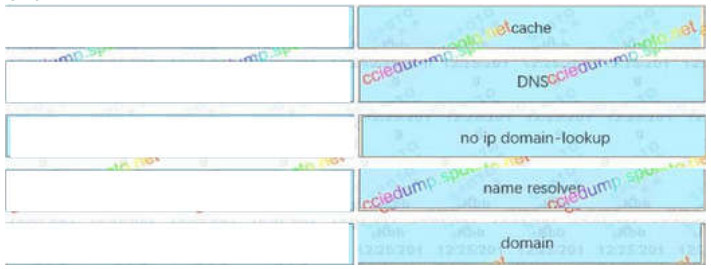
– Local database of accost mappings that improves proper noun-resolution performance : cache
– Service that maps hostnames to IP addresses : DNS
– Disables DNS services on a cisco device : no ip domain-lookup
– In response to client requests, queries a proper name server for IP address data : name resolver
– Component of e URL that indicates the location or organization type, such as .com or. edu : domain
50.
Elevate drop about RADIUS & TACACS+ 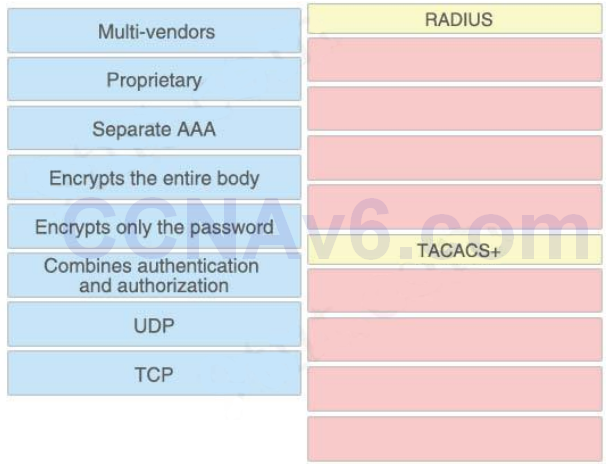
Answer:
RADIUS:
+ Multi-vendors
+ UDP
+ Combines authentication and authorization
+ Encrypts only the password
TACACS+:
+ Proprietary
+ Split AAA
+ Encrypts the unabridged torso
+ TCP
51.
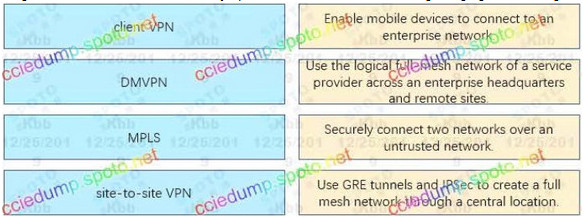
Correct Answer:

– Enable moble devices to connect to an enterprise network : client VPN
– Use the logical ful-mesh network of a service provider across an enterprise headquarters and remote stes : MPLS
– Securely connect two networks over an untrusted network. : site-to-site VPN
– Use GRE tunnels and IPSEC to create a ful-mesh network through a central location : DMVPN
52.
All nodes of Link Local –> FF02::ane
All EIGRPv3 Routers –> FF02::A
All OSPFV3 Designated Routers –> FF02::vi
All PIM Routers –> FF02::D
All OSPFv3 Routers –> FF02::5
All Routers of site local –> FF05::ii
53. Refer to the showroom
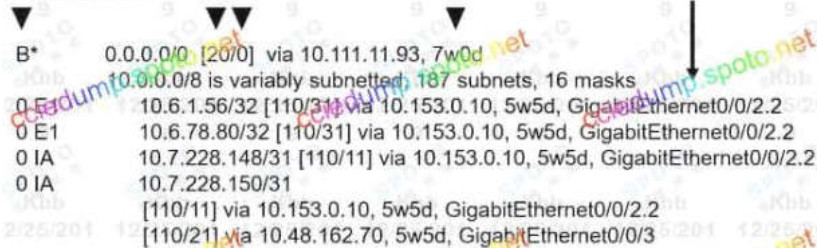
Drag and driblet the routing table components on the left onto the corresponding letter from the exhibit on the right. Not all options are used.
Select and Place – Your Response
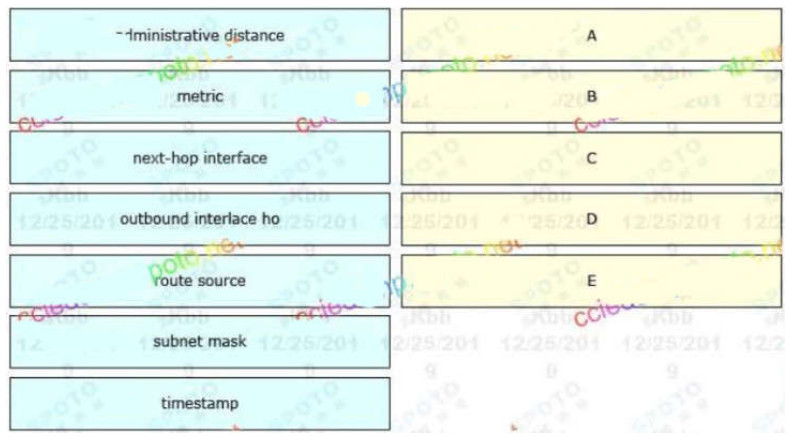
Correct Answer:
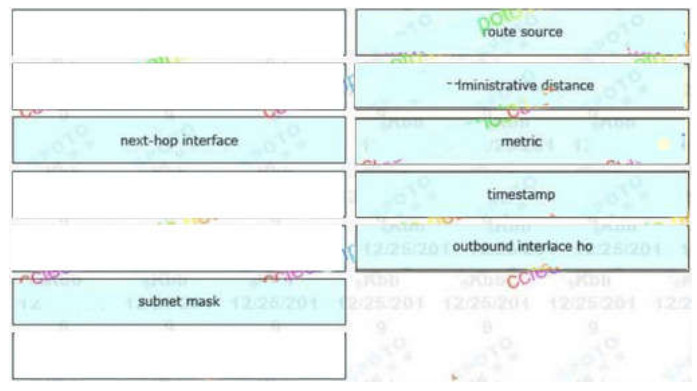
A: route source
B: administrative distance
C: metric
D: timestamp
Due east: outbound interlace ho
54. Drag and drop the source from the left to the numbers on the correct. Beginning with the lowest and catastrophe with highest administrative distance.
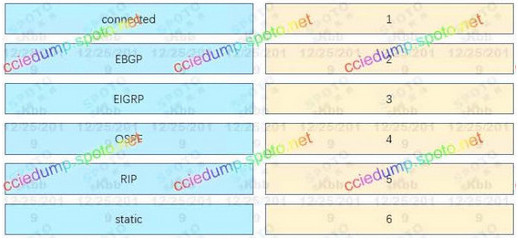
Correct Answer:
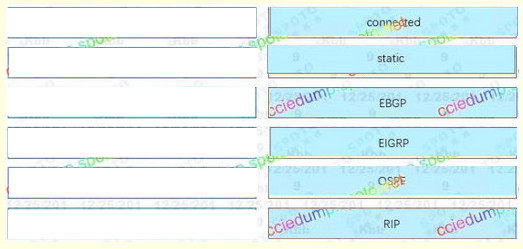
ane: continued
two: static
3: EBGP
iv: EIGRP
5: OSPF
6: RIP
55. You are configuration a switch so that it accepts traffic from a maximum of 2 dynamic MAC addresses. Drag and drop the required configuration commands on the left into the correct sequence on the right. (Not all commands are used)

Correct Answer:
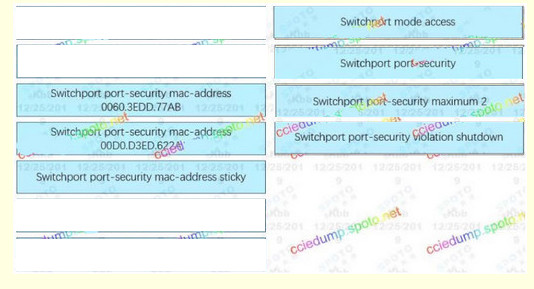
1: switchport style access
2: switchport port-security
3: switchport port-security mac-address sticky
4: switchport port-security maximum 2
Bear witness (Hide) Explanation/Reference
The full syntax of the second command is:
switchport port-security mac-address sticky [MAC]
If nosotros don't specify the MAC accost (similar in this question) and so the switch will dynamically learn the attached MAC Address and place it into your running-configuration
What Components Are Needed To Form A Dual-port 16-register File Of 8 Bits Each?,
Source: https://itexamanswers.net/ccna-200-125-drag-and-drop-questions-full.html
Posted by: duppstadtcosper.blogspot.com


0 Response to "What Components Are Needed To Form A Dual-port 16-register File Of 8 Bits Each?"
Post a Comment